Threat Intelligence
As modern cruise ships evolve into technologically advanced floating resorts, the intricate digital networks that manage everything from navigation to onboard entertainment have become both a critical asset and a potential vulnerability. Recognizing this, Royal Caribbean has recently updated its

The 2025 annual report from the interactive malware analysis platform ANY.RUN reveals a year of significant achievement and expansion, marking a pivotal period that not only scaled its user base to unprecedented levels but also introduced critical technological advancements in the fight against

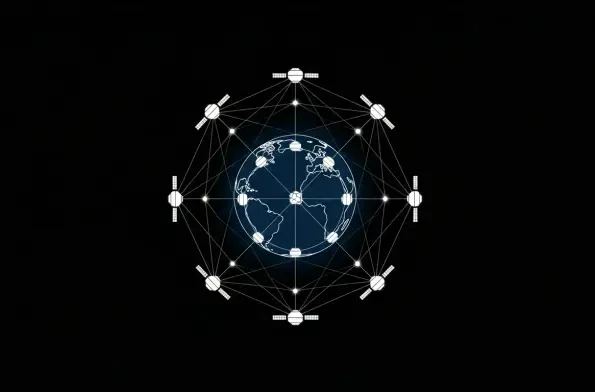
In the increasingly crowded and contested domain of Low-Earth Orbit, where thousands of satellites and pieces of debris travel at speeds exceeding 28,000 kilometers per hour, the window for responding to a potential threat is measured in minutes, not hours. Recognizing this critical vulnerability,
A simple text message arrives, presenting a unique investment opportunity from what appears to be a legitimate financial institution, an exclusive invitation that seems too good to pass up. This initial, unassuming contact serves as the gateway to an incredibly sophisticated and industrialized

The digital equivalent of decommissioning emergency sirens has just occurred across the federal government, marking a quiet yet profound evolution in the nation's cybersecurity defense posture. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has officially closed 10 Emergency
The digital landscape has evolved into a complex and treacherous battlefield where the lines between state-sponsored espionage, organized crime, and opportunistic exploitation have become dangerously blurred. A new paradigm of threat has emerged, one not defined by isolated hackers but by an














