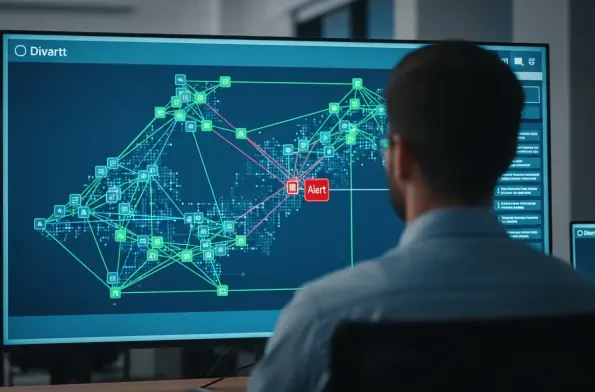
Threat Intelligence
In an increasingly interconnected world where digital infrastructure forms the backbone of government operations, the state of Texas has drawn a firm line in the sand against potential cybersecurity threats from foreign adversaries. The state recently moved to significantly expand its list of

The long-held playbook for digital marketing, meticulously crafted around the singular goal of achieving a top ranking on Google, is rapidly becoming obsolete in the face of a new technological titan. For years, securing that coveted first-page spot was the undisputed hallmark of success, a virtual

A single misconfigured regular expression within an essential AWS service recently stood as a silent, open gateway, potentially allowing attackers to launch a supply chain attack with the power to compromise the entire cloud ecosystem. This incident, now resolved, serves as a stark reminder of how

A seemingly straightforward function within the popular SmarterMail business email server has become the linchpin for a widespread campaign of cyberattacks, enabling unauthenticated threat actors to seize complete administrative control with alarming ease. Research from leading security firms

The Patch Paradox: When "Fixed" Isn't Fully Secure The recent revelation that fully patched Fortinet firewalls are being actively exploited has sent a chill through the cybersecurity community. For countless organizations, these devices are the first line of defense, making their
A security patch, once applied, is often considered the final word on a vulnerability, but recent events demonstrate that this assumption can create a dangerous blind spot for network administrators. This article investigates a new wave of automated attacks targeting FortiGate firewalls, focusing














