Threat Intelligence
The rapid deployment of Large Language Models within the modern security operations center has transitioned from a speculative experiment into a core operational necessity for identifying advanced persistent threats across global networks. While these systems possess an uncanny ability to ingest
The contemporary battlefield has transitioned into a digital-physical hybrid where the success of a kinetic strike often depends entirely on the precision of the cyber intelligence that preceded it. Military commanders no longer view digital operations as a secondary support function; instead, they
The traditional foundation of the Security Operations Center is experiencing a structural collapse as the velocity of machine-driven exploits begins to exceed the cognitive processing limits of even the most elite human analytical teams. Throughout the current landscape, the industry is witnessing
The Crisis: Velocity Without Visibility The global digital ecosystem currently faces an unprecedented paradox where the rapid acceleration of software production has directly compromised the structural integrity of the very systems designed to protect enterprise data. The core of the current
The sudden emergence of Claude’s Mythos Preview has fundamentally redefined the landscape of digital security by unleashing a relentless wave of automated vulnerability disclosures that traditional defensive structures are simply not equipped to handle. This technological leap has created a p

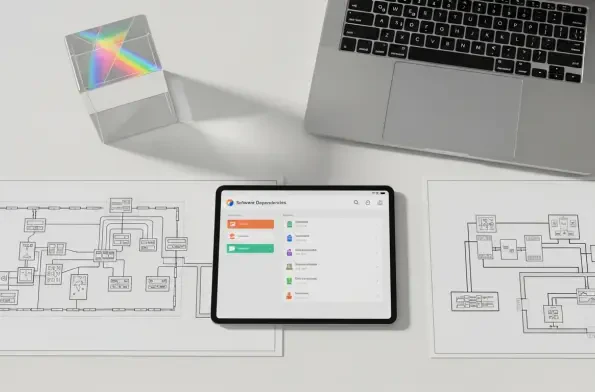
The contemporary digital landscape demands a level of vigilance that transcends traditional perimeter defenses, especially as enterprise ecosystems become increasingly entangled with third-party vendors and opaque supply chains. While many organizations rely on point-in-time assessments to judge

1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114













