Security in Digital Transformation
The rapid proliferation of sophisticated algorithmic threats has forced a total reevaluation of how global financial institutions protect their most sensitive data assets. As the boundary between traditional banking and digital infrastructure continues to blur, the integration of Artificial

As an expert in the field of physical security management and intelligent access control systems, Malik Haidar has spent years navigating the intersection of cybersecurity, physical intelligence, and enterprise risk strategy. With a background in securing multinational corporations, he understands

The sudden resurgence of the Pay2Key ransomware collective has sent ripples through the cybersecurity community, highlighting a sophisticated blend of traditional extortion and state-aligned disruption. While many ransomware groups operate with the singular objective of padding their digital

The Frontline of Home Defense: Why Router Security Is Non-Negotiable The silent sentinel of the digital age, a home router manages every byte of data entering a household while standing as the primary obstacle against relentless external threats. Modern networks have shifted from simple utilities
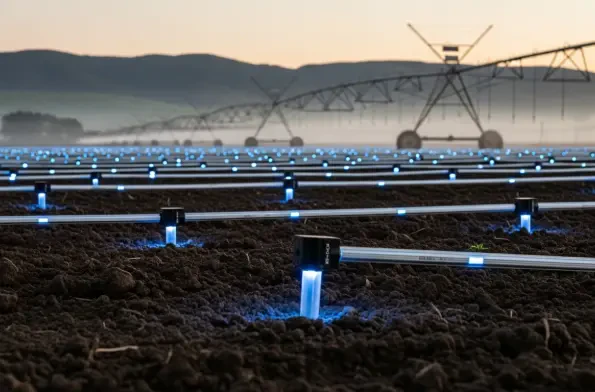
The rapid convergence of high-speed digital networks and heavy industrial machinery has created a landscape where a single lines of malicious code can now trigger catastrophic physical consequences. While a typical data breach in a corporate office might result in leaked emails or financial loss, a

Heavy industries are currently witnessing a seismic shift as they attempt to connect millions of disparate sensors across some of the most inhospitable and geographically isolated regions on the planet, creating a demand for infrastructure that moves beyond the limitations of traditional cellular