Security in Digital Transformation
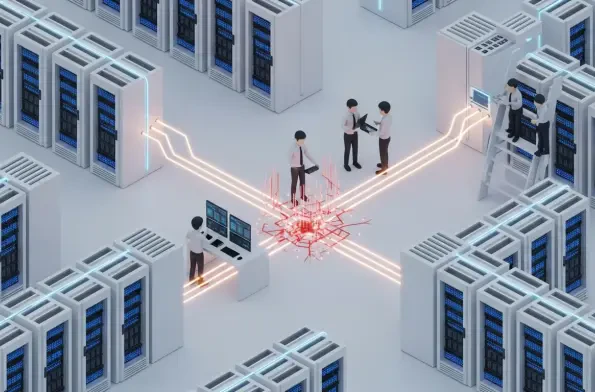
The very trust that underpins the seamless functionality of our interconnected digital world has become the most fertile ground for a new generation of sophisticated cyber attacks. As organizations increasingly rely on a complex web of integrated tools, platforms, and automated systems, adversaries
The window of opportunity for organizations to defend against newly discovered software vulnerabilities is closing at a breathtaking and unprecedented rate, fundamentally reshaping the dynamics of cyber defense. A critical analysis of recent threat intelligence reveals that the time between a
A sophisticated and rapidly spreading malware kit developed within China has begun systematically compromising hundreds of thousands of consumer and business-grade routers across the nation, creating a silent, sprawling botnet that poses a significant threat to the country's digital
A multimillion-dollar cybersecurity infrastructure, complete with the latest endpoint detection and response tools, can be systematically dismantled by a single file that predates the modern internet. This scenario is not theoretical; it represents a growing threat where attackers turn an operating

The coordinated cyberattack against European government institutions, which exploited critical vulnerabilities in Ivanti's mobile management software, has sent a clear and chilling message about the fragility of digital supply chains in the public sector. A sophisticated campaign struck at the
The seemingly legitimate job application sitting in a hiring manager's inbox, complete with a verified profile and convincing credentials, could be the digital key handed directly to a state-sponsored operative seeking to fund a nation's weapons program. This scenario is not theoretical;