Security Data Analytics
By the year 2026, the countless cameras that silently observe our public and private spaces will have undergone a profound transformation, evolving from passive recording devices into an intelligent, interconnected network capable of understanding the world in real time. This technological leap,

In the rapidly evolving world of cybersecurity, few voices stand out as much as Malik Haidar’s. With a career dedicated to protecting multinational corporations from sophisticated threats, Malik has become a beacon of insight, blending analytics, intelligence, and a keen business perspective into h

In a digital age where data is often called the new oil, a recent cybersecurity incident at Mixpanel, a prominent web and mobile analytics company, has exposed just how vulnerable that resource can be. Announced right before the U.S. Thanksgiving holiday, the breach, detected on November 8, has

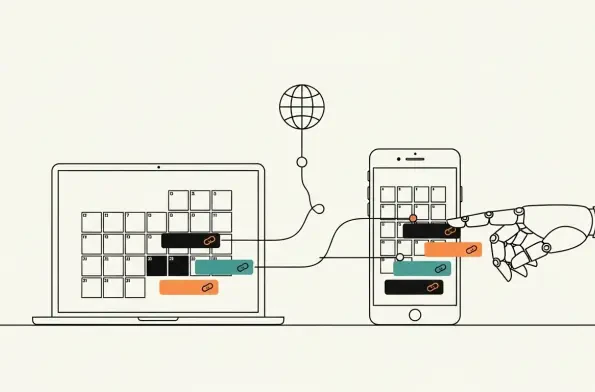
How legitimate calendar subscriptions enable scalable phishing and malware delivery Millions rely on calendar subscriptions for frictionless updates to holidays, school events, sports fixtures, and store promotions, yet the same convenience masks a quiet channel that continuously syncs in the
Cabin connectivity promised seamless service, but the reality is a crowded publish–subscribe network where dozens of vendors’ devices trade messages in milliseconds while quietly expanding an internal attack surface that traditional defenses do not touch. Transport encryption locks down links, and b

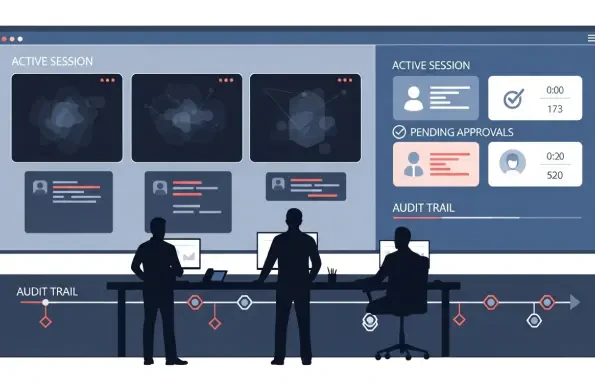
Insider incidents were climbing even as audit scrutiny tightened and workforces spread across clouds, contractors, and home offices, creating a dilemma that looked unsolvable without sacrifice. Security leaders felt pushed to choose between oversight and privacy, between control and speed, and