Security Data Analytics
The intricate architecture of modern software applications, assembled from a vast ecosystem of open-source libraries, third-party modules, and layers of transitive dependencies, has created an unprecedented challenge for cybersecurity. While this modular approach has been a catalyst for rapid
A staggering ninety-nine percent of organizations have reported experiencing at least one attack on their artificial intelligence systems within the last year, a statistic that underscores the immense and immediate security challenge accompanying the rapid adoption of AI. As businesses race to

Every Windows personal computer silently accumulates a detailed history of its usage, a digital chronicle of every installed application, every configured setting, and every connection made to the outside world. This history, often buried deep within the operating system, creates a complex and

A Critical Flaw Emerges in Cisco's Security Infrastructure In a stark reminder that even the most fortified digital perimeters are under constant siege, Cisco has issued a critical security warning for a previously unknown, or zero-day, vulnerability that is being actively exploited in

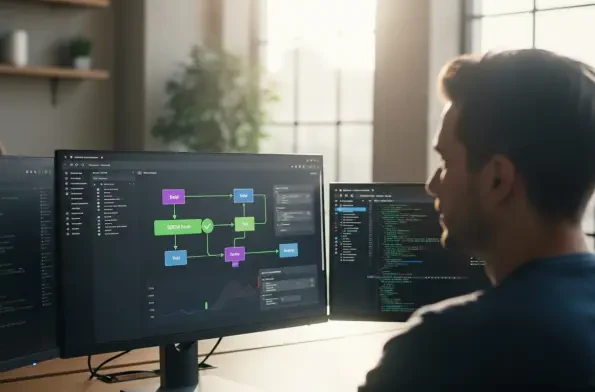
The artificial intelligence assistants once relegated to science fiction have quietly become standard issue in the corporate toolkit, creating an operational reality that has outpaced the security frameworks designed to protect it. Over the last year, nearly every major Software-as-a-Service (SaaS)

A massive data breach has cast a harsh spotlight on the fragile nature of digital privacy, exposing the deeply personal viewing habits of millions of Pornhub Premium users and igniting a firestorm of accusations between the companies involved. The incident centers on the alleged theft of an