Security Architecture
The modern enterprise cybersecurity landscape has become a complex tapestry of specialized tools, where an accumulation of best-of-breed products for identity, endpoints, and cloud security has inadvertently created a new, more insidious vulnerability. This fragmentation, a direct result of a
The long-established concept of a secure corporate network, protected by a strong digital perimeter, has become a relic of a bygone era, rendered obsolete by the realities of the modern, distributed business environment. Organizations no longer operate within clearly defined boundaries; instead,

As governments worldwide accelerate their digital transformation efforts, the challenge of securing vast and interconnected public-sector networks has become a paramount concern, prompting a search for more robust identity verification solutions. In a significant move to address this, BIO-key

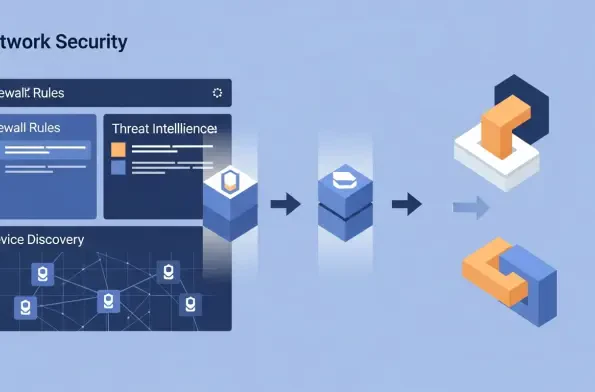
The latest major release of the open-source firewall platform, OPNsense 26.1, codenamed "Witty Woodpecker," marks a significant evolution in network security management by introducing a powerful API-driven architecture and a suite of new tools designed for modern IT environments. This
The modern enterprise security landscape often resembles a complex patchwork of specialized tools, each acquired to solve a specific problem, yet collectively creating a fragmented and overwhelming operational reality for security teams. This siloed approach, where endpoint protection, identity
The proliferation of smart home devices has quietly transformed the typical household network into a sprawling, unsecured digital landscape where every connected gadget, from your security camera to your coffee maker, can freely communicate with one another. This "flat" network














