Security Architecture
In a significant supply chain attack, the GitHub action tj-actions/changed-files was recently compromised, putting CI/CD pipelines and workflow secrets at risk. This attack highlights the vulnerabilities associated with third-party dependencies in continuous integration and continuous delivery
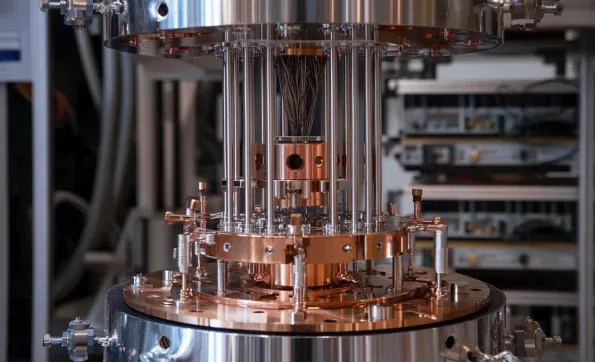
Quantum computing is advancing rapidly, presenting a real threat to conventional cryptographic systems. With the potential to render traditional encryption methods obsolete, it's imperative to understand these risks and prepare your data for the quantum era. Organizations must start taking
The evolving landscape of warfare and increasingly contested information environments have necessitated a transformative approach to the Army's cybersecurity and connectivity strategies. Released as a successor to the 2021 initiative, the Army Unified Network Plan (AUNP) 2.0 aims to

In yet another impressive display of financial prowess and innovative solutions, Zscaler Inc., a cloud security firm, reported a substantial leap in its fiscal 2025 second-quarter earnings and revenue. This performance has caught the attention of investors, leading to a significant surge in its

The cybersecurity landscape is rapidly evolving, with traditional perimeter-based models proving inadequate against increasingly sophisticated threats. As organizations face rising cyber risks, the need for more robust security frameworks becomes undeniable. This article delves into the concept of

With cyber threats becoming increasingly sophisticated and pervasive, the Australian government has rolled out new guidance to bolster IT network security for enterprises. This initiative, spearheaded by the Australian Signals Directorate's (ASD) Australian Cyber Security Center (ACSC), aims