Security Architecture
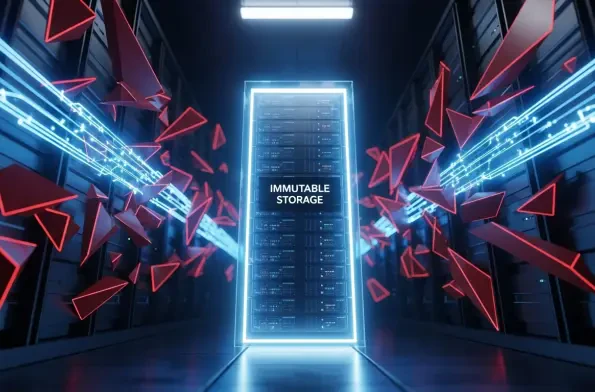
The assumption that a secure off-site backup serves as an impenetrable fortress against digital extortion has crumbled under the relentless pressure of autonomous malicious agents. For decades, organizations relied on the relative simplicity of data restoration to negate the leverage of
The modern enterprise is no longer defined by the physical walls of an office but by the digital threads of a software-defined fabric that connects global operations in real time. As organizations increasingly rely on centralized controllers like Cisco Catalyst SD-WAN to manage their vast networks,

The rapid migration from the automation-heavy focus of Industry 4.0 to the more holistic, human-centric values of Industry 5.0 has introduced a sophisticated set of challenges for global manufacturing networks. As industrial ecosystems evolve into hyper-connected environments where human operators
The traditional image of a security guard standing motionless at a gate is rapidly fading into the background as data-driven intelligence becomes the primary engine of modern safety protocols. Today, the global security landscape is undergoing a profound transformation, moving away from static

The long-standing tension between stringent cybersecurity measures and the demand for fast-paced, collaborative workflows has defined a critical challenge for modern enterprises. The integration of Privileged Access Management (PAM) into collaborative platforms represents a significant advancement

The lines once drawn by firewalls and network gateways have evaporated, leaving behind a digital landscape where the only constant, the only true defensible border, is the identity of who or what is accessing critical data. The cybersecurity industry has reached an inflection point, a moment