Security Architecture
Imagine a widely trusted tool, used by countless enterprises to process sensitive data, suddenly becoming a gateway for catastrophic cyber attacks. This is the alarming reality facing Apache Tika, a cornerstone framework for content detection and text extraction. With its critical vulnerability

Imagine a world where stepping into a high-security facility, a university campus, or even a hospital is as seamless as unlocking a smartphone, yet guarded by the most advanced identity verification technology available. This vision is inching closer to reality in Japan, thanks to a transformative

Imagine a world where cyber threats lurk in the shadows of every unchecked permission, waiting for the slightest lapse to strike at the heart of an organization’s security. This is the reality many enterprises face with standing privileges—those persistent, static permissions that often go unused or

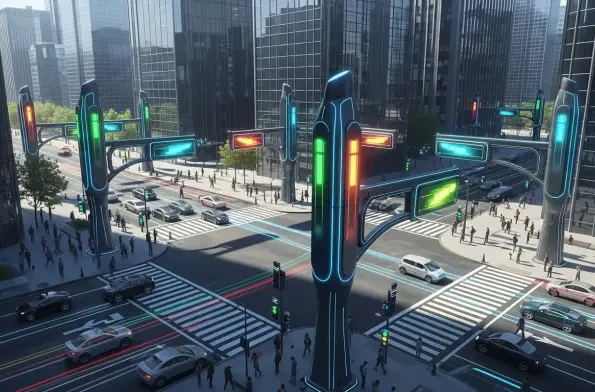
Imagine a world where power grids predict outages before they happen, water systems detect leaks in real-time, and transportation networks optimize traffic flow—all thanks to the power of artificial intelligence. This isn’t a far-off dream but a reality that critical infrastructure operators are beg
Imagine a government-owned entity, already marred by one of the UK's most infamous miscarriages of justice, accidentally exposing the personal details of hundreds of wronged individuals online. This scenario unfolded in 2024 when the Post Office leaked sensitive information of 502 postmasters
Diving into the fast-evolving world of cybersecurity, we’re thrilled to sit down with Malik Haidar, a seasoned expert who has spent years safeguarding multinational corporations from sophisticated cyber threats. With a deep background in analytics, intelligence, and security, Malik has a unique a














