Ransomware
Healthcare organizations are increasingly adopting Internet of Medical Things (IoMT) devices to enhance patient care and streamline operations. However, this rapid digital transformation comes with significant cybersecurity risks. Recent studies have revealed alarming vulnerabilities in these
Artificial Intelligence (AI) and data-driven technologies are revolutionizing cybersecurity strategies, creating dynamic shifts in how security measures are implemented and threats are mitigated. This transformation is critical as cyber threats become increasingly sophisticated and widespread. As

Understanding the evolving landscape of cyber threats is paramount for modern cybersecurity strategies. The dark web plays a crucial role in this domain, both as a marketplace for illicit activities and as a command center for cybercriminal operations. Through the lens of dark web intelligence,

In an era where cyber threats are on the rise, an international collaborative effort titled Operation Red Card was launched to tackle cyber-enabled fraud and online scams. This significant initiative, spearheaded by Interpol, spanned seven African countries: Benin, Côte d'Ivoire, Nigeria,
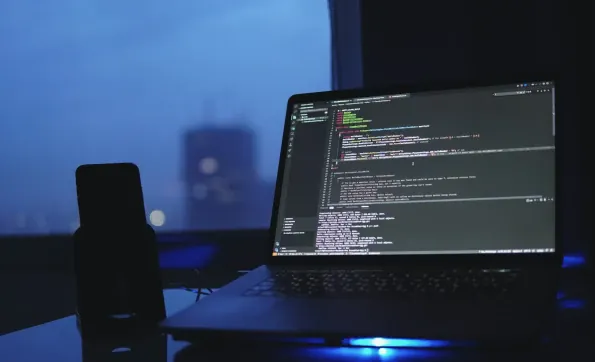
Penetration testing (pen testing) is an essential component in modern cybersecurity protocols. As cyber threats become more sophisticated, organizations must adopt dynamic methods to uncover and address vulnerabilities proactively. This article aims to explore the significance of pen testing in

In today's digital-first world, the demand for secure applications has never been higher. Cyber threats are growing in both sophistication and frequency, necessitating the adoption of advanced technologies to safeguard software. AI-powered malware detection leverages artificial intelligence to