Ransomware
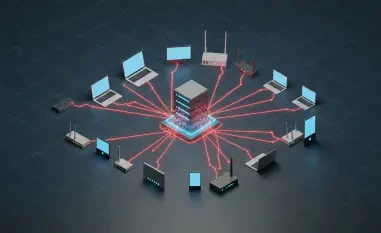
In an era where cyber threats evolve at an alarming pace, organizations grapple with the challenge of safeguarding their digital assets from adversaries who often operate in the shadows of hidden networks. The rise of sophisticated attacks, ranging from data breaches to targeted ransomware, has

In a striking development that has captured the attention of privacy advocates and lawmakers alike, three House Democrats have raised urgent concerns about a troubling contract between Immigration and Customs Enforcement (ICE) and an Israeli spyware firm, Paragon Solutions. This $2 million deal,

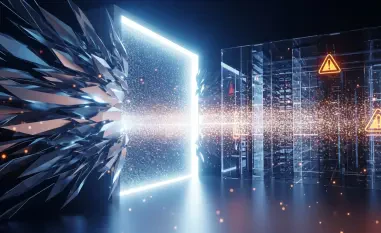
In today's digital arena, a single cyberattack can unravel years of business progress in mere hours, with damages often soaring into millions, making proactive measures essential. Consider a mid-sized retailer hit by ransomware on the eve of a major product launch—operations grind to a halt, c

Meet Malik Haidar, a seasoned cybersecurity expert with a wealth of experience in safeguarding multinational corporations from digital threats and hackers. With a deep background in analytics, intelligence, and security, Malik has a unique ability to blend business perspectives with cutting-edge

In an era where cyber threats evolve at a relentless pace, the tools designed to protect digital environments are sometimes turned against their very purpose, highlighting a critical challenge in cybersecurity. Consider the alarming reality that ransomware attacks have surged, with sophisticated

As the clock ticks down to the end-of-life date for Windows 10, a staggering number of users and organizations worldwide remain reliant on this operating system, raising serious concerns about cybersecurity in an increasingly hostile digital landscape. On October 14, Microsoft will officially cease