Network Security
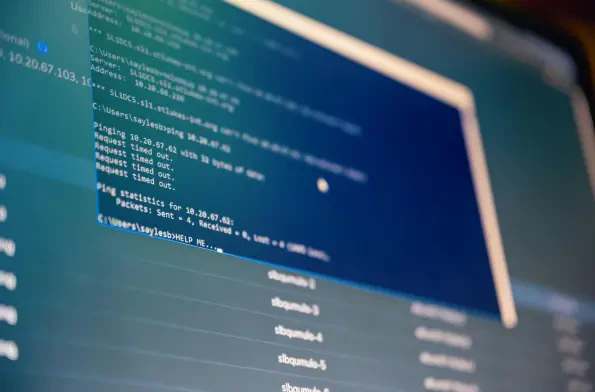
As cloud environments become increasingly integral to business operations, the risks associated with identity management and legacy vulnerabilities have surged to the forefront of cybersecurity concerns. Today, we’re thrilled to sit down with Malik Haidar, a seasoned cybersecurity expert with a d

I'm thrilled to sit down with Malik Haidar, a renowned cybersecurity expert with a wealth of experience safeguarding multinational corporations from digital threats. With a unique blend of analytics, intelligence, and security expertise, Malik has a keen understanding of how advanced network
In an era where digital battlegrounds are as critical as physical ones, a staggering reality emerges: European diplomats, entrusted with sensitive international negotiations, are under siege by sophisticated cyber espionage campaigns. Recent findings reveal a targeted operation by a group known as

I'm thrilled to sit down with Malik Haidar, a renowned cybersecurity expert whose career has been defined by his relentless fight against digital threats within multinational corporations. With a deep background in analytics, intelligence, and security, Malik has a unique ability to blend
In today’s fast-paced corporate world, imagine stepping up to an office door, turnstile, or elevator with nothing but a smartphone or smartwatch in hand—and gaining entry with a simple tap. This seamless experience is no longer a distant dream for employees at BNY, a global financial giant with a sp

Let me introduce Malik Haidar, a cybersecurity expert with a wealth of experience in protecting multinational corporations from sophisticated threats and hackers. With a deep background in analytics, intelligence, and security, Malik has a unique ability to blend business perspectives with