Emerging Threats
In a digital age where data is often called the new oil, a recent cybersecurity incident at Mixpanel, a prominent web and mobile analytics company, has exposed just how vulnerable that resource can be. Announced right before the U.S. Thanksgiving holiday, the breach, detected on November 8, has

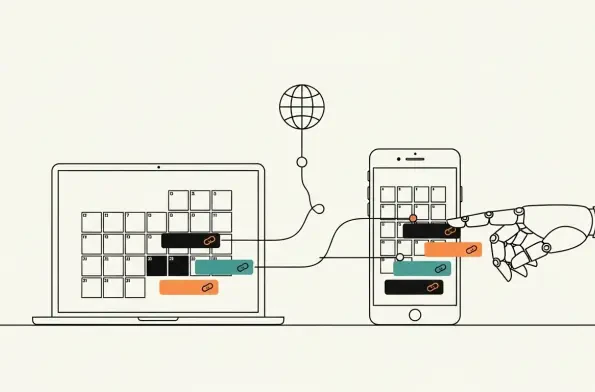
How legitimate calendar subscriptions enable scalable phishing and malware delivery Millions rely on calendar subscriptions for frictionless updates to holidays, school events, sports fixtures, and store promotions, yet the same convenience masks a quiet channel that continuously syncs in the
Unpacking the Ransomware Surge and Its Market Impact Imagine a digital battlefield where 85 distinct ransomware groups strike with relentless precision, targeting businesses across the globe, and racking up 1,590 victims in just one quarter. This staggering reality defines the ransomware landscape

Imagine a water treatment plant suddenly going offline, not due to a mechanical failure, but because a group of hacktivists has defaced its digital interface with political messages. This isn’t a far-fetched scenario but a growing reality in the world of cybersecurity, where industrial control s

I’m thrilled to sit down with Malik Haidar, a seasoned cybersecurity expert who has spent years on the front lines defending multinational corporations against sophisticated cyber threats. With a sharp focus on analytics, intelligence, and security, Malik brings a unique perspective by blending b

Cabin connectivity promised seamless service, but the reality is a crowded publish–subscribe network where dozens of vendors’ devices trade messages in milliseconds while quietly expanding an internal attack surface that traditional defenses do not touch. Transport encryption locks down links, and b