Emerging Threats
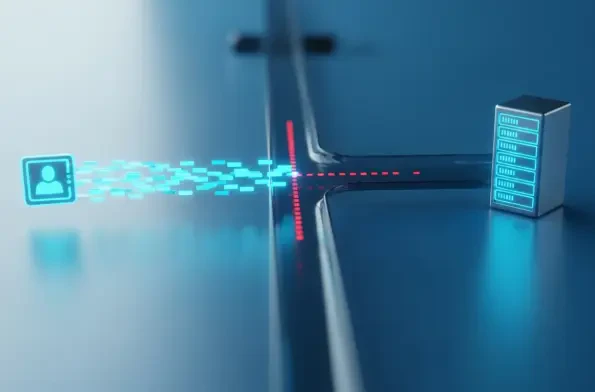
Introduction The sponsored links at the top of a search engine results page often seem like a shortcut to a trusted destination, but a recent international operation reveals they can also be the gateway to devastating financial fraud. The takedown of a sophisticated phishing website by the U.S.

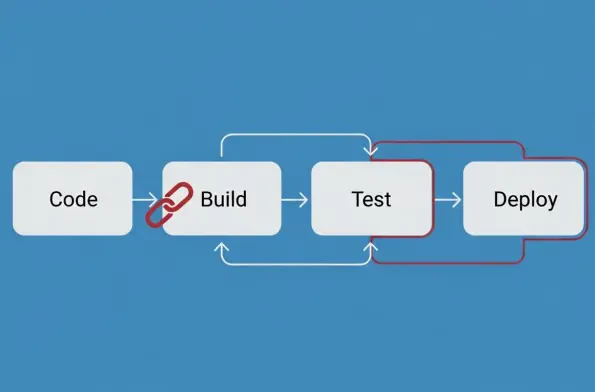
A recent, extensive analysis of software supply chains has brought to light a dangerously sophisticated and escalating threat targeting developers through widely trusted open-source repositories. This investigation uncovered two distinct but thematically linked campaigns that underscore a troubling

The very tools designed to enhance our online productivity and streamline digital workflows have become a sophisticated backdoor for cybercriminals to silently dismantle personal and enterprise security. Browser extension spyware represents a significant advancement in endpoint security threats,
The Rise of a New Threat Understanding the RondoDox-React2Shell Connection A persistent and increasingly sophisticated cyber threat known as the RondoDox botnet has been actively compromising Internet of Things (IoT) devices and web servers for over nine months, recently escalating its campaign by

As the initial frenzy surrounding artificial intelligence begins to mature, a more nuanced and strategic investment approach is emerging, compelling investors to look beyond the high-flying valuations of pure-play AI companies. The next chapter in this technological revolution calls for a pivot
The year 2025 will be remembered in cybersecurity circles not just for the record-breaking volume of new vulnerabilities disclosed but for the strategic precision with which threat actors exploited them to undermine the global software supply chain. An unprecedented surge in Common Vulnerabilities