Cybersecurity Investment
As the digital landscape expands at an unprecedented rate, organizations are grappling with an increasingly complex and porous attack surface, making the proactive management of cyber threats more critical than ever before. In a significant move to address this challenge, cybersecurity firm

The breathtaking speed at which artificial intelligence is reshaping our world is matched only by the unsettling quiet surrounding its profound and systemic security flaws. As large language models (LLMs) become more powerful and integrated into our daily lives, a critical examination of their
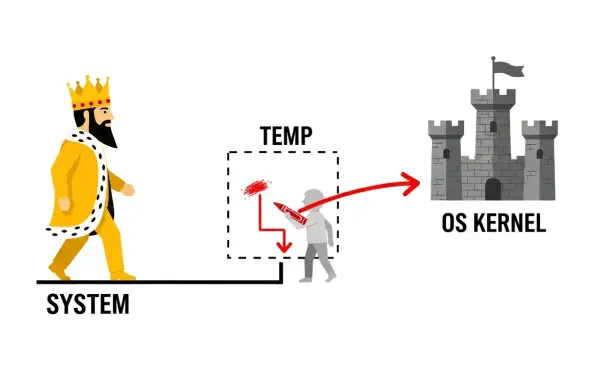
Introduction A seemingly harmless software uninstallation process can become the unlocked back door for an attacker, a reality recently underscored by a critical vulnerability discovered within the widely used JumpCloud platform. The platform, a cornerstone of IT management for thousands of
The healthcare payer information technology sector is undergoing a fundamental and rapid transformation, with the year 2026 emerging as a critical inflection point for execution and modernization. Survey findings from Black Book Research, involving over a thousand payer IT and administrative

A newly disclosed vulnerability in widely used web development frameworks is enabling unauthenticated attackers to achieve complete server compromise with a single, specially crafted web request, creating an urgent and severe risk for countless enterprise applications. Identified as React2Shell
The intricate digital infrastructures that underpin modern society are facing an unprecedented and increasingly sophisticated barrage of threats, forcing a critical re-evaluation of long-held security doctrines. Recent gatherings of top industry professionals have solidified a consensus that the














