Cybersecurity Investment
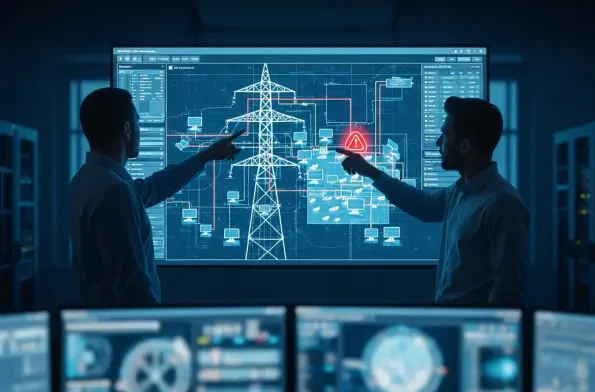
The very technology designed to secure Europe's energy future through clean, distributed power is quietly introducing a vulnerability that could bring the entire grid to a standstill. As solar panels blanket rooftops and fields in an unprecedented green transition, they are creating a vast,
The promise of AI assistants revolutionizing development workflows has collided with a stark security reality, exemplified by a critical vulnerability found within Docker's own Ask Gordon AI that forces a reevaluation of trust in automated tooling. This review examines the AI assistant not

The rapid digitalization of Mexico's logistics sector has forged a highly efficient and interconnected supply chain, yet this very connectivity has simultaneously created a landscape ripe with sophisticated and systemic cyber threats. As fleets integrate advanced telematics and cloud-based

The promise of a hyper-connected industrial landscape has long been tempered by the practical limitations of power consumption, often forcing a choice between the high performance of 5G and the low-energy profile of legacy 4G LTE. The 5G RedCap technology represents a significant advancement in the

The once-clear line between a safe digital interaction and a potential threat has blurred into an unsettling ambiguity, where the very tools and platforms designed to build confidence are now being systematically turned against their users. In a world saturated with digital services, the most
The most damaging security breaches often originate not from external hackers, but from trusted individuals who already possess authorized access to sensitive systems and data. This persistent and often overlooked vulnerability has prompted a significant response from the US Cybersecurity and














