Cyber Risk Management
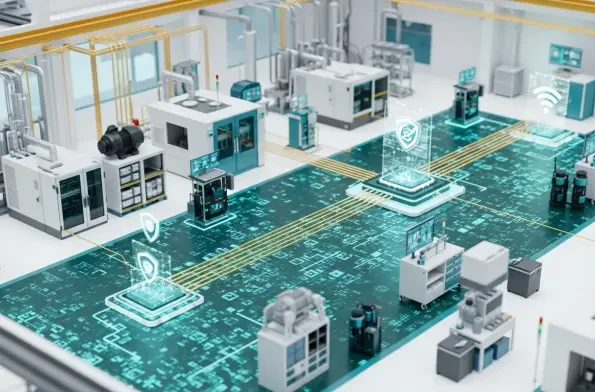
Malik Haidar is a veteran cybersecurity strategist who has spent years defending the digital perimeters of multinational corporations. His work sits at the intersection of high-stakes intelligence and business operations, focusing on how critical infrastructure can remain resilient in an era of
Understanding the Risk of Information Disclosure in Secure File Transfers A minor technical oversight in how a server processes session data can inadvertently provide attackers with the exact blueprint required to dismantle an entire enterprise security architecture. File transfer security is vital

The time between a software patch release and its active exploitation by malicious actors has effectively vanished, leaving security teams without the traditional luxury of defensive reaction. In 2026, the industry is grappling with a reality where the window of opportunity to secure systems is
The persistent recurrence of identical digital security breaches suggests that the global cybersecurity industry has spent billions of dollars merely to stand perfectly still. Despite the proliferation of sophisticated tools and record-high budgets, organizations frequently find themselves
The rapid migration of enterprise workflows into the web browser has created a paradox where the traditional firewall, once the ultimate arbiter of network security, now stands largely bypassed by the very traffic it was designed to govern. As modern employees spend the vast majority of their

The shifting landscape of modern cybersecurity now dictates that organizations must prioritize identity as the real perimeter rather than relying on legacy firewalls that attackers simply bypass using stolen but valid sign-in credentials. As the industry navigates the complexities of the current














