Cyber Risk Management
In a world where our entire lives are on our phones, the threat of mobile spyware has never been more immediate. We're joined today by Malik Haidar, a veteran cybersecurity expert who has spent his career on the front lines, battling sophisticated threats within major corporations. He's
System administrators faced a formidable challenge this February as a wave of critical security updates demanded immediate attention, headlined by Microsoft's disclosure of six zero-day vulnerabilities already being actively exploited in the wild. This sudden influx of patches, addressing a

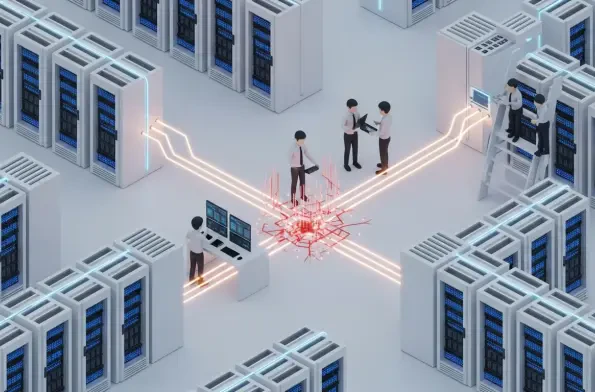
The coordinated cyberattack against European government institutions, which exploited critical vulnerabilities in Ivanti's mobile management software, has sent a clear and chilling message about the fragility of digital supply chains in the public sector. A sophisticated campaign struck at the
A recently disclosed vulnerability within the globally deployed Roundcube webmail software has demonstrated how obscure features in common web standards can be manipulated to completely neutralize fundamental email privacy protections. Security researcher Null Cathedral revealed a sophisticated

The very foundation of digital trust that underpins modern business communication is crumbling under the weight of an unprecedented wave of sophisticated, AI-driven cyber attacks that existing defenses were never designed to handle. A staggering 88% of organizations have suffered a security

The relentless drumbeat of vulnerability disclosures has security teams scrambling for a clear signal amidst the noise, and for many, the U.S. Cybersecurity and Infrastructure Security Agency's (CISA) KEV list has become that beacon. Since its inception, the catalog of Known Exploited