Cyber Defense Strategies
Welcome to an insightful conversation with Malik Haidar, a renowned cybersecurity expert with a wealth of experience in safeguarding multinational corporations from digital threats. With a deep background in analytics, intelligence, and security, Malik has dedicated his career to integrating

In a chilling revelation that underscores the growing sophistication of state-sponsored cyber threats, Microsoft has exposed a new espionage campaign orchestrated by the Russian state actor known as Secret Blizzard, specifically targeting foreign embassies based in Moscow. This operation, active

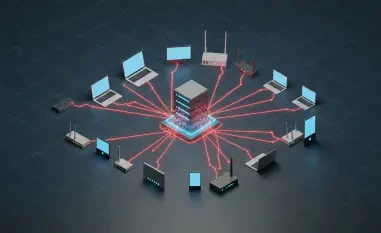
Diving into the Shadows of Cyber Warfare Imagine a world where foreign diplomats in a major global capital unknowingly surrender sensitive intelligence through their own internet connections, compromised at the very infrastructure level, revealing a chilling reality in Moscow. Here, a Russian

Overview of the Application Security Landscape Imagine a world where every digital interaction, from banking transactions to healthcare records, is under constant threat from invisible adversaries, and businesses must navigate this reality daily. As cyber threats escalate in sophistication and
In an era where cyber threats loom larger than ever, with global losses from cyberattacks projected to reach staggering figures, businesses face an uphill battle to safeguard their digital assets. A single breach can cripple operations, erode customer trust, and incur millions in damages, making

As digital landscapes evolve at a breakneck pace, system administrators (SysAdmins) stand as the unsung guardians of organizational security, a role celebrated annually on SysAdmin Day, July 25th. Their responsibility to protect critical systems and data has never been more vital, especially in the