Cyber Defense Strategies
Malik Haidar is a veteran cybersecurity expert who has spent years navigating the complex digital defenses of multinational corporations. With a background that seamlessly blends deep technical analytics with strategic business intelligence, he specializes in identifying how emerging technologies

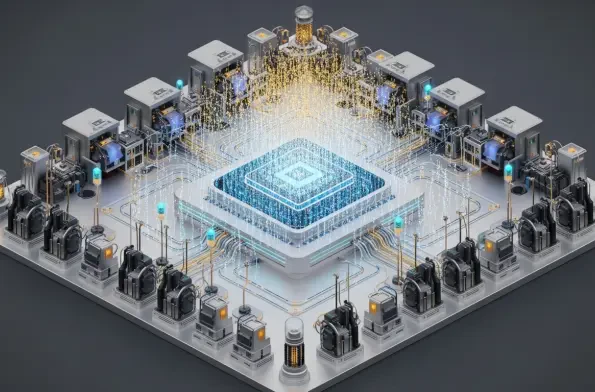
The rapid integration of sophisticated machine learning models into the daily workflows of global cyber adversaries has fundamentally altered the defensive requirements for modern digital infrastructure. As the current landscape evolves in 2026, the traditional boundaries between manual

The digital perimeter of the conflict in Ukraine has shifted from the localized energy grids of Kyiv to the highly secured servers of Western European financial institutions. While the world remains focused on the physical movement of troops, a more insidious campaign is unfolding within the

The rapid proliferation of sophisticated AI agents across corporate networks has introduced a formidable and stealthy security challenge, creating an environment where trusted automation tools can inadvertently become the most dangerous insiders. These AI systems, designed to streamline operations

Malik Haidar is a veteran cybersecurity expert who has spent years at the front lines of defense for multinational corporations, specializing in the intersection of threat intelligence and business-centric security strategy. His deep understanding of how state-sponsored actors manipulate everyday

The rapid migration from the automation-heavy focus of Industry 4.0 to the more holistic, human-centric values of Industry 5.0 has introduced a sophisticated set of challenges for global manufacturing networks. As industrial ecosystems evolve into hyper-connected environments where human operators