Cyber Defense Strategies
Escalating breach costs and headline ransomware incidents have made a hard truth unavoidable for leadership teams and auditors alike: backups that only exist as comfort blankets, untested and ungoverned, cannot be trusted to rescue business operations or pass scrutiny when controls fail and

Malik Haidar has spent the last decade running blue teams inside global enterprises, turning raw threat intelligence into business-aligned action. In this discussion, he opens the playbook behind a fast-moving response to Oracle Identity Manager’s CVE-2025-61757: scoping blast radius across SSO and

K–12 networks carried a growing weight of responsibility as classrooms, cafeterias, counseling, and payroll all leaned on the same digital backbone, yet attackers only needed one misstep to get in and spread. The security conversation in schools therefore shifted from promising perfect prevention t

In the high-stakes environment of air travel, where millions of passengers traverse bustling terminals daily, the imperative to safeguard lives and infrastructure against an ever-shifting array of threats has never been more pressing, and airports, as vital hubs of global connectivity, remain prime
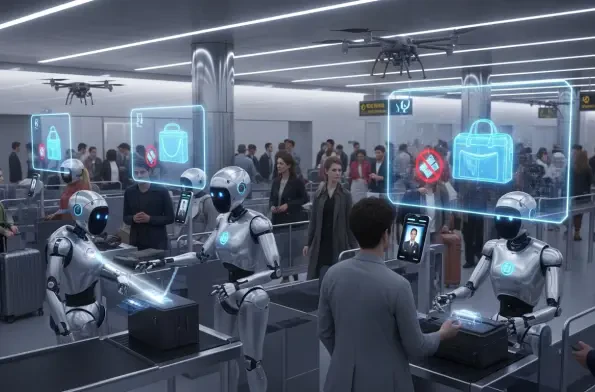
Artificial Intelligence (AI) is fundamentally transforming the realms of identity management and information security, ushering in a new era of innovation to tackle both immediate challenges and looming threats on the horizon. As enterprises increasingly integrate AI systems into their operations

In the rapidly evolving digital landscape, fintech startups face an ever-growing array of cybersecurity challenges that can threaten their survival, especially within the volatile realm of cryptocurrency platforms. A striking example of resilience in the face of such threats emerged recently when














