Cyber Defense Strategies
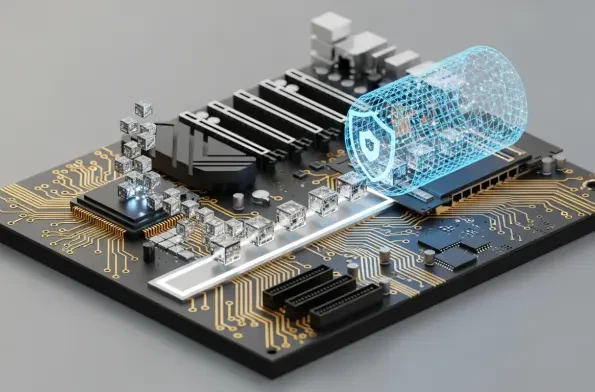
Data centers have profoundly evolved from being isolated, fortified structures into the hyper-connected and indispensable nerve centers of the global digital economy, demanding a radical rethinking of how these critical assets are secured. The long-standing model, which focused on building higher

The exciting prospect of sophisticated AI agents seamlessly managing complex online tasks on a user's behalf, from booking multi-leg trips to completing intricate application forms, is rapidly approaching reality. This functionality, often called "agentic browsing," promises a
The forthcoming Linux 6.19 kernel is set to introduce a landmark security enhancement that addresses a long-standing and often overlooked vulnerability at the very heart of modern computing: the unencrypted flow of data across internal hardware buses. For decades, the high-speed PCI Express (PCIe)
As artificial intelligence rapidly evolves from a sophisticated assistant into an autonomous operator at the core of enterprise functions, the fundamental principles of cybersecurity are being irrevocably altered. The traditional security perimeters built to safeguard networks and endpoints are

As decentralized networks grapple with the monumental challenge of securely onboarding millions of users, the bottleneck of identity verification has become a primary obstacle to growth and mainstream adoption. Addressing this critical juncture, the Pi Network has initiated a significant strategic

In the wake of a brazen abduction that saw numerous worshippers seized from a Cherubim and Seraphim Church during a sacred night service in Kogi State, Governor Ahmed Usman Ododo is now facing an intense and growing storm of public pressure. Community figures and religious leaders have issued