Cyber Defense Strategies
The delayed and frantic allocation of resources following a security breach represents a common, yet entirely avoidable, organizational failure that transforms a preventable risk into a catastrophic financial event. As businesses increasingly entrust their most sensitive operations to

In the vast and often opaque world of digital application stores, ensuring the security of the software we install can feel like an act of faith, but a new, data-driven tool is set to replace that faith with verifiable facts for users of the Snap ecosystem. Created by Ubuntu alumnus Alan Pope, a
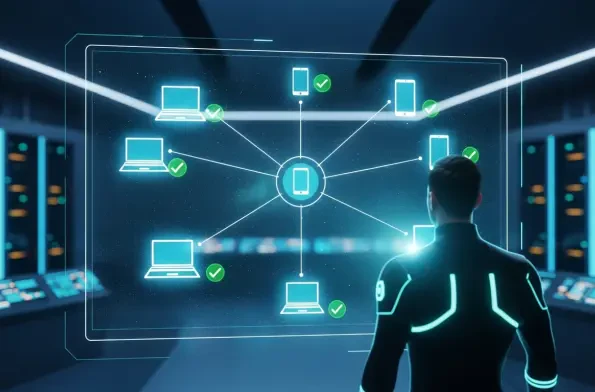
A leading Fortune 50 automotive manufacturer, navigating the complexities of a sprawling multi-cloud infrastructure across Amazon Web Services, Microsoft Azure, and Google Cloud Platform, found its security aspirations and operational agility severely constrained by its outdated Privileged Access
The modern enterprise landscape is a complex tapestry of distributed endpoints, hybrid work models, and an ever-expanding attack surface, creating a significant challenge for IT and security teams who often find themselves juggling a disparate collection of siloed tools. In response to this growing
In the escalating battle against digital adversaries, the ability of threat actors to cloak their true location using anonymizing services has become a formidable obstacle for security teams worldwide, leaving organizations vulnerable to infiltration from seemingly legitimate sources. Preemptive

A comprehensive journalistic investigation conducted in Austria has brought to light a sophisticated, multi-country disinformation campaign orchestrated by a pro-Russian agent network with direct ties to Russia's Federal Security Service (FSB). This clandestine operation was meticulously














