Cyber Defense Strategies
A digital attack from halfway around the world can cripple a nation's infrastructure, a reality underscoring the borderless nature of modern security threats. In this ecosystem, international collaboration is a strategic necessity. However, a major U.S. policy shift now raises fundamental

In the rapidly evolving industrial sector where the adoption of AI-driven systems and autonomous vehicles is accelerating, Cisco has distinguished itself by winning two prestigious IoT Breakthrough Awards for its forward-thinking solutions. The accolades for Cisco Ultra-Reliable Wireless Backhaul

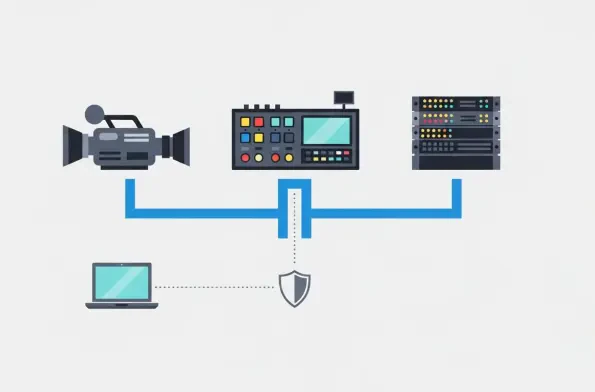
The unforgiving nature of live broadcasting, where a single dropped frame can disrupt an experience for millions, has long relied on a security model of physical isolation, but this approach has become dangerously obsolete in an interconnected, IP-driven world. While the corporate IT sector has
In today's complex digital environments, the concept of permanent access privileges has become a significant liability, creating persistent vulnerabilities that threat actors are all too eager to exploit. Cybersecurity giant CrowdStrike Holdings Inc. has unveiled a definitive agreement to

The digital landscape is perpetually besieged by evolving cyber threats, yet few have achieved the notorious efficiency and market dominance of the LockBit ransomware operation. Emerging from the shadows in 2019, this Ransomware-as-a-Service (RaaS) syndicate has consistently refined its tools and
The U.S. Department of Defense is facing a monumental challenge as it races against a critical 2027 deadline to overhaul its cybersecurity infrastructure, a task so vast that traditional human-led methods are proving to be a significant bottleneck. At the heart of this strategic shift is the Zero














