Compliance & Regulations
The digital equivalent of decommissioning emergency sirens has just occurred across the federal government, marking a quiet yet profound evolution in the nation's cybersecurity defense posture. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has officially closed 10 Emergency
The digital clock of a modern enterprise does not just measure productivity; it now ticks down the minutes and millions lost while recovering from an inevitable cyber-attack, a period of downtime that can quickly escalate into an existential crisis. In this landscape, cyber resilience—the ability t
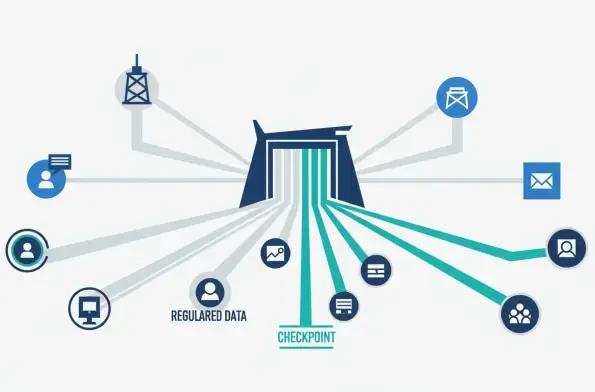
The digital landscape across Greater China is undergoing a seismic regulatory shift, as both Beijing and Hong Kong have decisively moved to fortify their data and cybersecurity frameworks with a host of new laws and stringent enforcement measures. The start of 2026 signals a significant maturation
The recent death of Aldrich Ames, the notorious CIA officer who spied for the Soviet Union and later Russia, serves as a stark and timely reminder that the most devastating security threats often originate not from sophisticated external attacks, but from within an organization's own trusted
The seemingly secure environment of popular communication platforms has been compromised by a sophisticated, Python-based malware known as VVS Stealer, which actively targets Discord users with a formidable array of stealth and data theft capabilities. This malicious software, which has been in
The intricate web of satellite communications, navigation, and Earth observation systems that underpins modern society is facing an increasingly complex and nebulous regulatory challenge from a cybersecurity perspective. While the critical importance of protecting these space-based assets is