Compliance & Regulations
Seasoned UK security leaders are stepping away from the CISO chair at a pace that should alarm any board responsible for safeguarding revenue, reputation, and critical operations across increasingly digital businesses facing relentless adversaries and hardening regulations. The exit is not a blip;

Market Overview: The Cyber Threat Landscape In an increasingly interconnected world, a chilling statistic sets the stage for concern: 41% of cybersecurity professionals in the US and UK identify data loss as their paramount fear when facing state-sponsored cyber-attacks. This alarming figure

Imagine a small rural clinic, bustling with patients seeking care, unaware that their most sensitive personal health information (PHI) is just a click away from falling into the wrong hands. Cyberattacks on healthcare facilities are no longer a distant threat but a stark reality, with breaches

Small businesses with lean teams and tight margins have increasingly found that a single cyber incident can knock out core systems, disrupt sales, and trigger a costly scramble to recover, even when the breach started with nothing more than a phish or a misconfigured account exposed to the

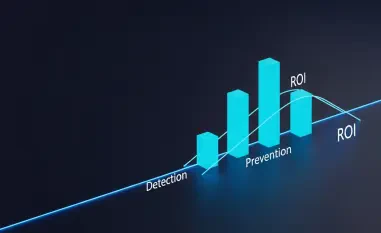
Escalating breach costs and headline ransomware incidents have made a hard truth unavoidable for leadership teams and auditors alike: backups that only exist as comfort blankets, untested and ungoverned, cannot be trusted to rescue business operations or pass scrutiny when controls fail and

Why a supplier’s slip can ripple across an airline’s ecosystem News that a vendor breach exposed Iberia customer names, emails, and Iberia Plus IDs jolted security teams because it revealed how familiar details can be weaponized even when passwords and cards stay safe. Several airline CISOs noted th