Advanced Threat Protection
In the ever-evolving landscape of cybersecurity, staying ahead of vulnerabilities in widely used tools is crucial. Today, we’re speaking with Malik Haidar, a seasoned cybersecurity expert with a deep background in protecting multinational corporations from digital threats. With his extensive e

In an era where digital warfare is as critical as physical combat, the U.S. Army's Next Generation Command and Control (NGC2) platform has emerged as a pivotal tool in modernizing military operations, only to face significant cybersecurity hurdles in its early prototype stage. Designed to

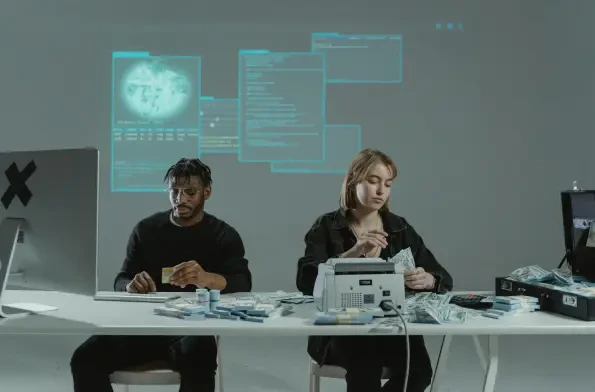
In a striking demonstration of judicial resolve, a Chinese court has handed down severe penalties to 16 members of a notorious crime syndicate based near the Myanmar border, spotlighting the escalating battle against transnational cyber fraud. The Ming family, operating from the Kokang region in

In a startling development this September, a severe cybersecurity threat has emerged with the active exploitation of zero-day vulnerabilities in Cisco Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) software, which are critical components of network security infrastructure used

Imagine a world where a single click from an unsuspecting employee could cost a company millions in damages due to a cleverly disguised cyberattack, a scenario that is becoming all too common as cybercriminals leverage advanced AI to craft personalized scams that exploit human error, often the

In today’s digital landscape, where cyber threats are an ever-present danger, financial advisors, particularly registered investment advisors (RIAs), face immense pressure to protect client data under stringent regulations like the U.S. Securities and Exchange Commission (SEC) cybersecurity rule. T