Advanced Threat Protection
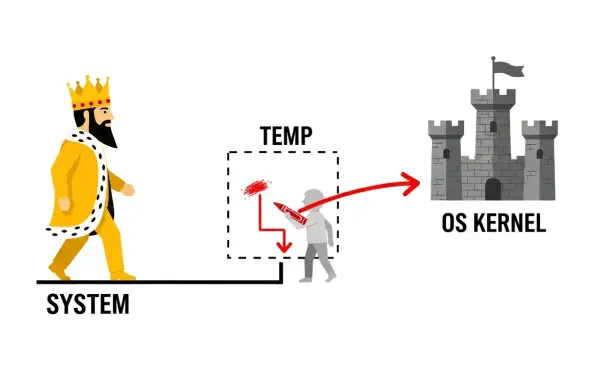
The administrative tools that system administrators rely on for daily operations are built on a foundation of trust, where elevated permissions are granted to perform necessary tasks efficiently and securely. However, a recently discovered vulnerability in JumpCloud Remote Assist for Windows,
The very code that promises to build the future is now being written with the help of automated assistants that can inadvertently open doors for sophisticated digital adversaries, transforming the software supply chain into the modern era's most critical battleground. This evolution marks a

The recent disclosure of the critical remote code execution vulnerability CVE-2025-55182, dubbed React2Shell, sent shockwaves through the development community, not just for its maximum possible CVSS score of 10.0 but also for its alarming ease of exploitation. Within days of the patch release by

A seemingly harmless file shortcut, an icon millions of users click daily without a second thought, became the hidden key for international espionage groups to unlock sensitive networks across the globe for nearly a decade. This was not a complex, code-breaking exploit but a simple deception rooted
In a digital landscape where open-source collaboration and shared tools are the bedrock of modern software creation, a newly uncovered series of attacks is weaponizing the very foundation of developer trust. A comprehensive analysis has brought to light a sophisticated, multi-platform threat

Vast repositories of encrypted government data are being silently collected by adversaries today, with the full expectation that the arrival of a quantum computer will soon provide the key to unlock every secret they contain. This looming reality transforms the abstract threat of quantum computing