Advanced Threat Protection
The breathtaking speed at which artificial intelligence is reshaping our world is matched only by the unsettling quiet surrounding its profound and systemic security flaws. As large language models (LLMs) become more powerful and integrated into our daily lives, a critical examination of their
A critical security flaw has been identified within the widely-used Motors WordPress theme, creating a direct path for a complete site takeover on more than 20,000 active automotive websites, fundamentally undermining their digital security. This significant vulnerability, officially cataloged as
The very digital infrastructure designed to support global commerce and government services is being methodically transformed into a weaponized network by sophisticated threat actors, turning an organization's own assets against others. This escalating trend represents a formidable shift in
The familiar red flags of cyber scams, such as glaring grammatical errors or suspicious sender addresses, are rapidly becoming relics of a bygone era as criminals now wield powerful artificial intelligence tools to craft attacks with unprecedented sophistication. What used to be easily identifiable

A frantic phone call shatters the quiet of an afternoon, the voice on the other end a perfect, panicked replica of a loved one pleading for immediate financial help—a scenario that has become terrifyingly common and is now the central target of landmark legislation moving through the U.S. Senate. T

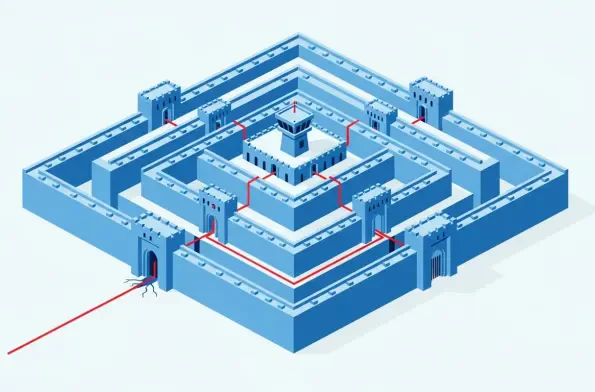
The digital perimeter that once clearly defined corporate security has dissolved into a complex and borderless ecosystem, placing an unprecedented burden on the very tools designed to protect it. In this new reality, the Next-Generation Firewall (NGFW) has evolved from a simple gatekeeper into the