Advanced Threat Protection
International cybersecurity agencies have issued a stark warning regarding a critical vulnerability in MongoDB, now under active exploitation, which poses a significant and immediate threat to organizations utilizing exposed database infrastructure across the globe. Cybersecurity authorities in

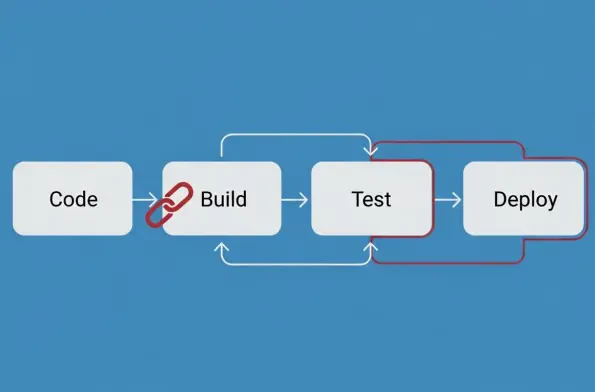
The year 2025 will be remembered in cybersecurity circles not just for the record-breaking volume of new vulnerabilities disclosed but for the strategic precision with which threat actors exploited them to undermine the global software supply chain. An unprecedented surge in Common Vulnerabilities
The once-obscure technical document known as the Software Bill of Materials has become one of the most debated and divisive artifacts in the entire cybersecurity landscape, fundamentally altering how organizations procure, develop, and deploy software. By 2026, the discussion is no longer about

The widespread adoption of artificial intelligence within security operations centers has paradoxically created a landscape where advanced tools often exist without a clear purpose or measurable impact. While the promise of AI-driven threat detection and automated response has captivated the

Operating from the deepest recesses of a computer's operating system where security software rarely has the final say, a newly discovered weapon has fundamentally altered the cyber espionage landscape and redefined the meaning of digital stealth. A sophisticated, previously undocumented

A sophisticated cyberattack on the popular Chinese short-video platform Kuaishou recently exposed approximately 85 million live-stream viewers to a barrage of abusive and violent material, signaling a potentially seismic shift in the nature of digital threats. The incident, which lasted for about














