International cybersecurity agencies have issued a stark warning regarding a critical vulnerability in MongoDB, now under active exploitation, which poses a significant and immediate threat to organizations utilizing exposed database infrastructure across the globe. Cybersecurity authorities in both the United States and Australia are urging immediate action as attackers are actively leveraging the flaw, tracked as CVE-2025-14847 and colloquially named “MongoBleed,” to compromise sensitive systems. The U.S. Cybersecurity & Infrastructure Security Agency (CISA) has underscored the severity of the situation by mandating that all federal civilian agencies apply the necessary patches by January 19. This directive is mirrored by concerns from the Australian Signals Directorate, which has confirmed its awareness of widespread global exploitation attempts, signaling a coordinated international effort to contain the fallout from this dangerous security loophole.
1. The Nature of the Threat
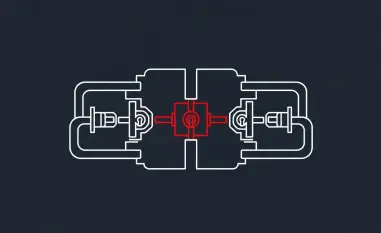
The MongoBleed vulnerability is technically classified as an improper handling of length parameter inconsistency, originating from a deep-seated flaw in the way MongoDB Server processes zlib-compressed network messages. At its core, a defect within MongoDB’s decompression logic can be triggered by a malicious actor, causing the database to inadvertently return segments of uninitialized heap memory to a remote client. Crucially, this data leakage can occur before any authentication process is initiated, effectively leaving the door wide open for unauthenticated attackers. An adversary with network access to the MongoDB port can repeatedly send specially crafted requests to the server, methodically probing it to aggregate these leaked memory fragments. Over time, this process can allow the attacker to reconstruct and expose highly sensitive information, including user credentials, active session keys, internal system state data, and other proprietary information that should remain strictly confidential, providing a powerful vector for deeper network intrusion.
The timeline of this vulnerability’s exploitation demonstrates the speed at which modern cyber threats can escalate from a theoretical possibility to a tangible global risk. A proof-of-concept (PoC) exploit code was made publicly available on GitHub on December 25, and within a matter of days, security researchers began detecting a significant uptick in automated scanning and active exploitation attempts targeting vulnerable MongoDB instances. This rapid weaponization highlights a concerning trend in the cybersecurity landscape where the gap between vulnerability disclosure and mass exploitation is shrinking dramatically. Further analysis indicates that the scale of exposure is vast, with tens of thousands of MongoDB deployments remaining publicly accessible on the internet and therefore susceptible to attack. The problem is compounded by the fact that zlib compression, the feature at the heart of the vulnerability, is a common default configuration, meaning many systems are vulnerable without any specific, non-standard changes having been made by administrators, thus broadening the potential attack surface significantly.
2. Scale of Exposure and Expert Analysis
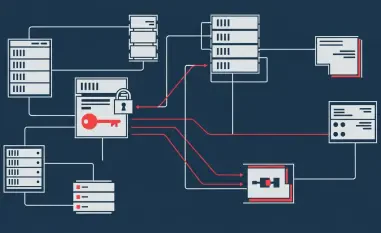
The potential impact of the MongoBleed vulnerability is staggering, with network scanning services identifying approximately 87,000 MongoDB instances worldwide that could be susceptible to this form of attack. This widespread exposure is not limited to on-premises servers; cloud security telemetry has revealed that a substantial portion of cloud environments host at least one affected database, placing a diverse range of industries and organizations at risk. The global nature of the threat is what prompted the coordinated response from CISA and the Australian Signals Directorate. CISA’s binding operational directive, which sets a firm deadline for federal agencies to remediate the vulnerability, serves as a clear indicator of the perceived risk to national infrastructure and government operations. This firm stance is intended to not only secure federal networks but also to set a strong precedent for the private sector, encouraging organizations of all sizes to prioritize patching and mitigation efforts before they fall victim to an attack that is already being actively carried out by malicious actors on a global scale.
Security experts have drawn parallels between MongoBleed and other infamous memory disclosure vulnerabilities, such as the 2014 Heartbleed bug, to emphasize the potential severity of the flaw. Dan Andrew, head of security at Intruder Systems Ltd., highlighted that this is a serious vulnerability enabling an unauthenticated remote attacker to retrieve information directly from MongoDB’s memory. Similar to previous heap disclosure vulnerabilities, the ultimate impact of exploitation will inevitably vary depending on the specific information an attacker manages to extract from the compromised system’s memory heap. However, the probability remains high that the leaked memory will contain valuable assets like authentication credentials or other sensitive data. This risk is expected to grow as attackers continue to learn more about the vulnerability and refine their exploitation techniques to more effectively target and extract the most critical information, potentially leading to full system takeovers, extensive data breaches, and severe reputational damage for affected organizations.
3. A Forward-Looking Security Posture
In response to the active exploitation campaigns, MongoDB has released official patches to address the flaw across all of its supported versions, and security defenders are being strongly urged to upgrade their systems without delay. The primary and most effective remediation strategy is the immediate application of these patches to eliminate the vulnerability at its source. However, for organizations that are unable to apply the patches immediately due to operational constraints or complex deployment environments, cybersecurity agencies have outlined several crucial mitigation steps. The most prominent of these recommendations is to disable zlib compression, which directly neutralizes the attack vector. Additionally, organizations are advised to implement strict network access controls, ensuring that MongoDB instances are not exposed to the public internet and that access is restricted exclusively to trusted hosts through firewalls or similar security controls. This layered approach of patching and hardening provides a robust defense against the immediate threat posed by MongoBleed.
The emergence and rapid exploitation of the MongoBleed vulnerability served as a critical reminder of foundational cybersecurity principles. Expert analysis concluded that, regardless of patch status, database systems like MongoDB should never have been directly exposed to the open internet. The incident underscored the vital importance of a defense-in-depth strategy, where security is not reliant on a single control but is instead composed of multiple, overlapping layers. Best practices, such as rigorously employing firewalls, implementing strict network segmentation to isolate critical systems, and consistently minimizing the attack surface, were proven to be essential for robust protection. Ultimately, while immediate patching was a necessary tactical response, the MongoBleed event highlighted a broader strategic lesson: a proactive and comprehensive security posture, built on established principles of secure architecture, was the most effective defense against both this specific threat and the countless others that will inevitably follow.