In the current landscape of the mid-2020s, the traditional boundaries of corporate security have completely dissolved, replaced by a complex environment of cloud applications, decentralized networks, and physical facilities. As human vulnerabilities intersect with increasingly sophisticated digital threats, the role of Identity and Access Management (IAM) has shifted from a mere back-office function to a core strategic necessity for any organization. This shift demands a move away from static, siloed defenses toward a more integrated, AI-driven model that treats every access point as a potential vector for a breach.
Navigating this new era requires an understanding that the security perimeter is no longer a physical wall but a dynamic layer of identity verification. Modern organizations must contend with the fact that an intruder in a server room is just as dangerous as a hacker on the network. Consequently, the integration of digital and physical security has become the only viable path toward operational resilience and legal protection. By centering security strategies on the individual rather than the device or the badge, companies can better address the fluid nature of modern threats.
Navigating the New Era of Identity and Access Management
The security challenges of the present day are defined by a fusion of high-tech deception and persistent human error. Organizations are no longer just protecting data; they are protecting the very integrity of identity itself. As remote work and hybrid office models have become standard, the surface area for potential attacks has expanded exponentially, making legacy access control methods obsolete. This environment necessitates a fundamental rethinking of how trust is established and maintained across an entire enterprise.
Strategic necessity now dictates that identity management must be proactive rather than reactive. Waiting for a breach to occur before updating security protocols is a recipe for disaster in a fast-paced market. Modern IAM systems must be capable of analyzing massive amounts of data in real time to ensure that only authorized personnel have access to specific resources at specific times. This holistic approach ensures that security serves as an enabler of business rather than a bottleneck, fostering a culture where safety and productivity coexist.
Why AI-Driven Security Modernization Is Essential for Survival
Transitioning to an AI-powered security framework has become a fundamental requirement for business continuity in a world where threats evolve daily. The primary benefit of this shift lies in the ability to move from a defensive posture to a predictive one, where anomalies are identified before they escalate into full-scale incidents. By automating the detection of subtle patterns that human operators might overlook, organizations can significantly reduce incident response times and mitigate risks that legacy systems are simply not designed to handle.
Modernization also serves as a critical defense against mounting legal liabilities. Courts and regulatory bodies now frequently apply the “foreseeability” standard, which suggests that if a threat is well-documented, an organization has a duty to implement reasonable measures to prevent it. Failing to adopt state-of-the-art technologies can be construed as negligence, leading to multi-million dollar settlements and irreparable reputational damage. Therefore, investing in AI-driven security is as much about legal protection as it is about technical defense.
Best Practices for Implementing AI in Identity and Access Control
To effectively combat modern threats, organizations must move beyond simple credential validation and embrace a holistic, identity-centric approach. This involves integrating disparate security systems into a cohesive whole that provides a 360-degree view of every individual’s activity. These actionable steps provide a clear roadmap for any business looking to harden its defenses through the power of artificial intelligence and machine learning.
Bridge the Gap Between Physical and Digital Security Silos
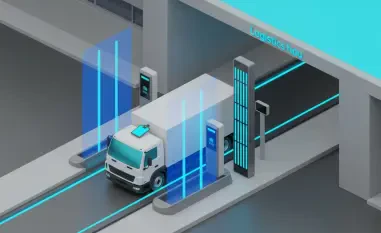
The first step in modernizing access control involves the convergence of physical and cyber security into a unified management framework. Historically, these two departments operated in isolation, often using different software and reporting to different leadership teams. By correlating data from physical entry points with digital network activity, AI tools can create a singular defense perimeter that recognizes a threat regardless of whether it originates at a server cabinet or a login screen.
Moreover, this convergence allows for a more nuanced understanding of user behavior. If a user’s badge is used to enter a building in New York, but their digital credentials are simultaneously used to log in from London, a unified system can flag this impossible travel scenario instantly. This level of cross-domain intelligence is impossible to achieve when physical and digital data are stored in separate databases, making integration a top priority for any security-conscious organization.
Case Study: Preventing Lateral Movement Through Unified Analytics
A global financial firm demonstrated the power of this integration by linking its biometric door logs with its network monitoring software. When the AI detected a physical entry into a secure satellite office while the same user’s credentials were simultaneously being used to access a sensitive database from a different city, the system reacted without human intervention. It automatically locked the digital account and alerted on-site security, preventing a coordinated data exfiltration attempt that would have succeeded under a siloed management structure.
Combat Human Error With AI-Enhanced Anti-Tailgating Technology
Tailgating remains a leading cause of security breaches because legacy badge readers validate the card rather than the person holding it. Implementing AI-driven sensors and biometric verification at high-traffic entry points removes the reliance on employee politeness and ensures that every individual entering a facility is authorized. This technology moves the burden of enforcement from the individual employee to an automated system that is immune to social engineering and distraction.
Furthermore, AI-powered systems can distinguish between a person carrying a heavy box and an unauthorized individual attempting to slip through a closing door. By providing real-time alerts and high-definition video evidence of tailgating events, security teams can identify repeat offenders and address cultural weaknesses within the workforce. This shift from social compliance to strict identity verification significantly hardens the physical perimeter of any corporate campus or data center.
Case Study: Reducing Physical Breaches in High-Traffic Lobbies
A technology campus struggling with “polite” tailgating at its main entrance deployed AI-powered facial recognition equipped with tailgating detection. Within the first quarter of operation, the system identified and blocked over two hundred unauthorized entries that would have previously gone unnoticed. This transition effectively shifted the security culture toward a more rigorous standard, where employees understood that the system, not their colleagues, was responsible for managing access.
Neutralize Synthetic Media With Liveness Detection
As deepfakes and AI-generated spoofing have become more accessible to bad actors, visual verification has had to evolve to maintain its integrity. Incorporating “liveness detection” ensures that the identity being presented to a scanner is a living, breathing human being rather than a high-resolution photograph or a digital reproduction. This technology is essential for maintaining the integrity of biometric authentication in an age where high-quality synthetic media can be generated in seconds.
Liveness detection works by analyzing subtle cues such as micro-expressions, blood flow patterns in the skin, and the natural movement of the eyes. These features are incredibly difficult for synthetic media to replicate convincingly at a hardware level. By making liveness detection a standard part of the authentication process, organizations can neutralize one of the most sophisticated tools in the modern hacker’s arsenal and ensure that biometric markers remain a reliable form of identity.
Case Study: Defending Against Sophisticated Identity Spoofing
During a targeted social engineering attack, an intruder attempted to use a high-definition synthetic video on a tablet to bypass a facility’s facial recognition scanner. However, the system’s liveness detection algorithms identified the lack of natural depth and blood flow patterns inherent in the fake media. The system immediately triggered an alarm and locked down the sensitive area, proving that AI-driven defenses were the only effective way to counter the rise of AI-driven deception.
Strengthening the Organizational Security Posture
The evolution of AI provided a powerful toolkit for solving the identity challenges that had plagued organizations for decades, offering a level of precision previously thought impossible. Technology proved most effective when it was paired with a security-conscious culture and a commitment to continuous policy evolution. This integrated approach became particularly beneficial for high-risk industries, such as healthcare and finance, where the cost of a breach was historically catastrophic.
Before adopting these technologies, leaders evaluated their existing infrastructure for compatibility and prioritized systems that offered multifactor authentication and real-time threat intelligence. By making these strategic investments, organizations transformed their security from a point of vulnerability into a pillar of proactive resilience. The shift toward automated, identity-centric management ultimately allowed businesses to focus on growth while maintaining a robust defense against an ever-changing threat landscape.