Modern state-sponsored actors have moved far beyond the rudimentary phishing emails of the past, now embedding their malicious operations within the very cloud ecosystems that global enterprises rely on for daily productivity. This evolution represents a fundamental shift in the digital arms race, where the boundary between a harmless spreadsheet and a weaponized command-and-control node has effectively vanished. As organizations migrate their most sensitive workflows to the cloud, groups like UNC2814 have recognized that the best place to hide a secret is in plain sight, specifically within the trusted encrypted traffic of major service providers.
The Evolving Landscape of State-Sponsored Cloud Exploitation
The traditional reliance on dedicated malware servers is rapidly giving way to a “living off the cloud” philosophy that exploits the inherent reputation of established platforms. By utilizing legitimate infrastructure, attackers ensure their communication remains indistinguishable from routine business operations, making the task of perimeter defense nearly impossible for standard security protocols. This strategy has allowed sophisticated actors to maintain a persistent presence within the telecommunications and government sectors of over 40 countries, turning the interconnected nature of the global economy into a strategic vulnerability.
Threat actors like UNC2814 prioritize these high-value sectors because they provide access to vast amounts of metadata and personal communications. The strategic significance of targeting the digital backbone of a nation cannot be overstated, as it grants foreign intelligence services a window into both diplomatic movements and private citizen behavior. Consequently, major technology conglomerates find themselves thrust into a dual role, acting as the essential service providers for modern society while simultaneously serving as the primary intelligence agencies responsible for hunting advanced persistent threats.
Technical Innovations and Market Impact of the GridTide Campaign
Stealth Through Integration: The Rise of Command-and-Control via Google Sheets
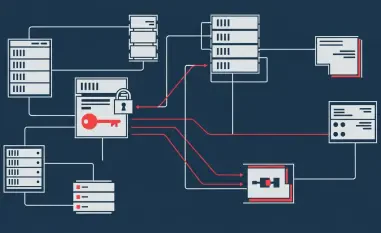
At the heart of this disruption is the “GridTide” backdoor, a sophisticated piece of engineering that transforms the Google Sheets API into a covert communication channel. Instead of connecting to a suspicious IP address, the infected host sends requests to a legitimate Google URL, effectively masking the transmission of shell commands and exfiltrated data. This integration means that network defenders see nothing more than a developer or analyst updating a document, a common activity that rarely triggers an automated alert or manual investigation.
The shift toward targeting compromised web servers and edge systems as initial access points further complicates the defensive landscape. By exploiting vulnerabilities in unpatched external hardware, UNC2814 establishes a foothold that is difficult to dislodge without significant operational downtime. While other entities like Salt Typhoon exhibit similar interests in telecommunications data, the specific operational signatures of GridTide—including its unique exploitation of cloud-native APIs—mark it as a distinct and highly specialized threat in the current espionage market.
Data-Driven Surveillance Trends and the Growth of Cyber-Espionage
Market data indicates a projected surge in state-sponsored surveillance, with a specific focus on the systematic monitoring of activists and high-ranking officials. With at least 53 confirmed victims identified in this recent disruption, the actual global reach of the campaign likely encompasses hundreds of hidden points of entry. The impact is quantified not just in lost intellectual property, but in the compromise of call records and unencrypted SMS messages, which provide a granular view of a target’s life and associations.
Exfiltration trends have moved toward a more aggressive collection of metadata that can be analyzed over long periods. Measuring the success of a disruption involves tracking the time it takes for an adversary to re-establish these connections; however, the immediate shutdown of the GridTide infrastructure provides a necessary reprieve for targeted organizations. The long-term viability of such espionage hinges on the attacker’s ability to remain undetected, a metric that is now being challenged by proactive cloud monitoring and rapid incident response.
Navigating the Obstacles of Defending Open Cloud Ecosystems
Defending an open ecosystem requires a delicate balance between security and functionality, as the very features that empower developers are often the ones exploited by attackers. Distinguishing between a legitimate API call and a malicious command is a monumental task when both originate from authenticated accounts and follow the same syntax. This trust gap is widened by standard encryption, which protects user privacy but also provides a dark corner where state-sponsored actors can operate without fear of casual inspection.
Identifying persistent threats that have remained active since the late 2010s requires a deep historical analysis of network behavior and a willingness to question the integrity of trusted streams. Revoking API access or shutting down projects is a high-stakes decision for cloud providers, as any error could result in the accidental disruption of critical business operations for legitimate global clients. Technical hurdles remain significant, particularly when attempting to patch vulnerabilities in legacy edge systems that are no longer supported by their original manufacturers.
Regulatory Responses and the Security of Legitimate API Frameworks
International cybersecurity standards are beginning to reflect the reality of cloud abuse, forcing providers to implement more rigorous monitoring of their own internal APIs. Compliance now demands that intrusions by state-sponsored actors be reported with greater transparency to government partners, fostering a more collaborative environment for threat intelligence. Strengthening Identity and Access Management (IAM) is no longer just a best practice; it has become a mandatory shield against the unauthorized creation of cloud projects used for illicit command-and-control activities.
The role of collaborative intelligence sharing is becoming the cornerstone of a unified front against advanced persistent threats. By pooling data from various sectors, defenders can identify patterns that would be invisible to a single entity. This cooperative approach helps establish a baseline for what constitutes normal API behavior, making it easier to spot the subtle deviations that characterize a sophisticated breach. As regulatory pressure mounts, the expectation for cloud providers to police their platforms has shifted from a voluntary effort to a core requirement of digital citizenship.
The Future of Cyber-Defense in an Era of Persistent Threat Actors
The expected resurgence of UNC2814 suggests that the battle for cloud security is far from over, as these actors possess the resources to rebuild their infrastructure with even greater complexity. Future defensive strategies will likely lean heavily on AI-driven traffic analysis to detect the faint “noise” created by anomalous behavior within supposedly trusted streams. This technology promises to identify malicious intent by analyzing the timing and frequency of API calls, providing a layer of security that transcends traditional signature-based detection.
A transition toward Zero Trust architectures is becoming the standard for any organization handling sensitive government or telecommunications data. In this model, no internal or external communication is inherently trusted, regardless of whether it originates from a reputable service like Google or Microsoft. This shift represents a fundamental change in how the industry views connectivity, prioritizing verification at every step to ensure that a spreadsheet remains just a spreadsheet and not a gateway for foreign intelligence.
Strengthening Global Resilience Against Sophisticated Espionage
Google’s decisive action to dismantle the GridTide command structure successfully neutralized a significant threat to global telecommunications and diplomatic integrity. The intervention demonstrated that cloud providers possess the unique visibility required to identify and terminate sophisticated C2 channels that bypass traditional network security. These events confirmed that the creative exploitation of legitimate services is now a primary tactic for state actors, necessitating a move toward more granular monitoring of API-based communications across all organizational levels.
Security teams were encouraged to implement more rigorous audits of cloud project creation and API usage to catch unauthorized activity in its early stages. The resolution of this campaign provided a clear roadmap for how private-sector intelligence can effectively partner with international entities to protect the digital supply chain. Moving forward, the industry adopted a more skeptical stance toward “trusted” traffic, ensuring that future attempts to weaponize cloud productivity tools would be met with immediate and automated resistance.