Malik Haidar is a veteran cybersecurity strategist who has spent years defending the intricate nerve centers of multinational corporations. With a deep background in threat intelligence and infrastructure security, he specializes in the intersection of business continuity and aggressive defense. His recent work has focused heavily on the architectural vulnerabilities of software-defined networking, making him a critical voice in understanding the current crisis surrounding the Cisco SD-WAN zero-day.
The conversation explores the technical mechanics of the CVE-2026-20127 vulnerability, the tactical evolution of “leapfrog” exploitation, and the immense logistical pressure placed on organizations by global security mandates. We also delve into the strategic shift required to validate network integrity when the very fabric of the SD-WAN has been compromised by unauthorized administrative access.
Given that CVE-2026-20127 carries a maximum CVSS score of 10.0, how does this specific authentication bypass exploit peering mechanisms? What are the immediate risks of an attacker gaining administrative privileges through NETCONF, and how does this compromise the entire SD-WAN fabric?
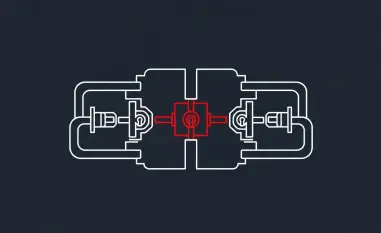
The gravity of a 10.0 CVSS score cannot be overstated because it implies that the front door to your network is essentially unlocked for anyone who knows how to turn the handle. In this case, the vulnerability stems from a failure in the peering authentication mechanism between the Catalyst SD-WAN Controller and the Manager, allowing an unauthenticated remote attacker to masquerade as a legitimate part of the system. Once they send those crafted requests and bypass the gate, they gain access to a high-privileged, non-root internal account. The real danger unfolds when they use this account to access NETCONF, a protocol designed for installing and manipulating the configuration of network devices. By gaining this foothold, an attacker can rewrite the rules of the entire SD-WAN fabric, redirecting traffic, intercepting sensitive data, or even isolating entire branch offices from the data center with a few lines of code.
Threat actors are reportedly downgrading systems to exploit legacy vulnerabilities like CVE-2022-20775 before restoring the original software to hide root access. Why is this “leapfrog” technique so effective against modern defenses, and what forensic indicators should teams look for when hunting for these persistent intruders?
This “leapfrog” or “downgrade” technique is a masterclass in psychological and technical deception because most monitoring tools are tuned to look for the “new” rather than the “old.” By temporarily rolling back the system to an older version, the attacker re-opens a door—CVE-2022-20775—that the organization thought they had closed years ago, allowing them to escalate their privileges to root. Once they have that ultimate level of control, they restore the modern software version, effectively burying their tracks and leaving the administrator believing the system is up-to-date and secure. When hunting for these intruders, forensic teams must look for anomalies in the system logs, specifically unexpected version changes or reboot cycles that don’t align with scheduled maintenance windows. It is also vital to audit the internal user accounts for any “high-privileged” activity that doesn’t correspond to a known administrative ticket or authorized configuration change.
With major security agencies setting tight deadlines for patching, what logistical hurdles do organizations face when securing connectivity between branch offices and data centers? How does the insertion of a “malicious rogue peer” complicate the process of validating network integrity and removing persistent threats?
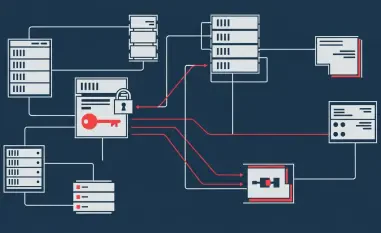
The logistical pressure is immense, especially with agencies like CISA setting deadlines as tight as February 27, 2026, because SD-WAN is the backbone of connectivity for modern enterprises. You aren’t just patching a single server; you are updating the orchestration layer for potentially hundreds of branch offices and data centers, where any downtime can halt business operations entirely. The insertion of a “malicious rogue peer” makes this a nightmare because it means the threat is now an “insider” within the network’s trusted architecture. This rogue device acts as a silent parasite, and even after you patch the software, the device may still be recognized as a legitimate member of the fabric. Validating integrity requires a grueling process of re-authenticating every single peer in the network and comparing current configurations against a known-good baseline to ensure no unauthorized tunnels or routing paths were created during the compromise.
Beyond applying patches, why is it necessary to implement secondary controls like perimeter filtering and session timeout adjustments? What specific steps should a security team take to differentiate between legitimate administrative traffic and malicious manipulation of the SD-WAN Manager or Controller?
Patching is only the first step because it fixes the hole, but it doesn’t necessarily evict the squatter who already climbed through it. Secondary controls like perimeter filtering act as a “safety net,” ensuring that even if an authentication bypass exists, the attacker cannot reach the management interface from the public internet. Tightening session timeouts and enhancing logging are sensory upgrades; they help us catch the “twitchy” behavior of a bot or an intruder who is moving faster or differently than a human admin would. To differentiate legitimate traffic from manipulation, security teams should implement strict IP whitelisting for all administrative access and monitor NETCONF traffic for unusual patterns or bulk configuration exports. If you see administrative commands coming from a location or at a time that doesn’t match your operational schedule, you must treat it as a high-priority breach until proven otherwise.
What is your forecast for SD-WAN security?
I believe we are entering an era where the “infrastructure as code” nature of SD-WAN will become the primary target for state-sponsored and sophisticated criminal groups, shifting the focus from attacking individual PCs to attacking the very pathways that connect them. In the coming years, we will see a massive push toward “Zero Trust” peering, where the identity of every controller and edge device is continuously verified using hardware-rooted keys rather than just static credentials or vulnerable handshakes. We should also expect a surge in AI-driven behavioral analytics that can spot the subtle, non-root manipulations that current signature-based defenses miss. Ultimately, organizations will have to treat their network fabric as a living, breathing entity that requires constant health checks, moving away from the “set it and forget it” mentality that has plagued networking for decades.