The rapid migration from the automation-heavy focus of Industry 4.0 to the more holistic, human-centric values of Industry 5.0 has introduced a sophisticated set of challenges for global manufacturing networks. As industrial ecosystems evolve into hyper-connected environments where human operators and autonomous systems collaborate in real-time, the vulnerabilities inherent in the Industrial Internet of Things become increasingly pronounced. Traditional cybersecurity frameworks, which once relied on rigid perimeter defenses and reactive patching, are no longer sufficient to protect the intricate web of sensors, actuators, and controllers that power modern infrastructure. This shift necessitates the adoption of Digital Twin technology, a revolutionary approach that creates high-fidelity virtual replicas of physical assets. By synchronizing real-world data with digital models, organizations can achieve a level of visibility that transforms security from an afterthought into a foundational element of the industrial design process. This evolution emphasizes systemic resilience and environmental sustainability, ensuring that manufacturing processes are not only efficient but also inherently robust against the growing spectrum of cyber threats that target critical infrastructure in 2026.
Simulation Strategies: Creating Risk-Free Defense Environments
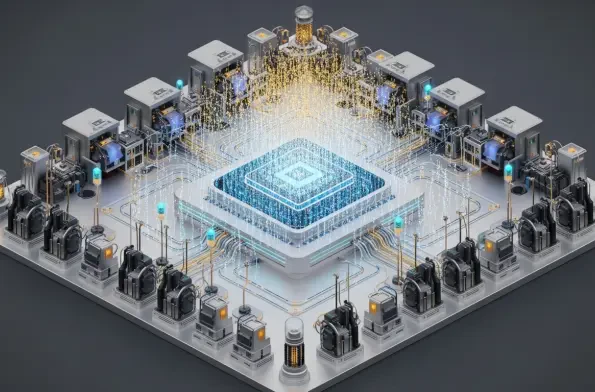
One of the most transformative applications of Digital Twin technology lies in its ability to facilitate extensive threat modeling within a strictly controlled and isolated virtual sandbox. Security professionals can now orchestrate a wide range of malicious activities, such as Distributed Denial-of-Service attacks, sophisticated ransomware injections, and Man-in-the-Middle exploits, to observe exactly how these threats propagate through a complex network. This foresight allows engineers to identify hidden bottlenecks and critical points of failure without risking the integrity of physical machinery or interrupting active production lines. By running these high-stakes simulations in a digital mirror, teams can develop and refine automated containment strategies that trigger the moment an anomaly is detected in the real world. This proactive stance ensures that the physical system remains resilient, even when faced with the type of multi-vector cyberattacks that have become increasingly common as industrial networks become more decentralized.
Beyond the realm of hypothetical simulation, the Digital Twin functions as a continuous verification node that significantly enhances the overall reliability of the modern industrial ecosystem. By comparing a constant stream of real-time data from physical sensors against a strictly authorized digital profile, the system can immediately flag any minor discrepancies that might indicate data injection exploits or unauthorized equipment tampering. This real-time situational awareness is vital for maintaining operational continuity, particularly in sectors where even a few seconds of downtime can result in massive financial losses or safety hazards. The ability to isolate compromised network segments while allowing the rest of the facility to function normally represents a major leap forward in industrial logic. Instead of a total system shutdown, which was often the only recourse in the past, modern factories utilize their digital replicas to perform surgical interventions that neutralize threats while preserving the flow of production.
Technological Integration: Enhancing Twins with AI and Blockchain
The effectiveness of Digital Twins in the realm of cybersecurity is significantly amplified when these virtual models are integrated with advanced Artificial Intelligence and Machine Learning algorithms. These analytical tools are capable of processing the vast, heterogeneous streams of data generated by the Industrial Internet of Things to establish precise behavioral baselines for every machine on the floor. By understanding what constitutes normal operation down to the millisecond, the AI-driven twin can detect subtle deviations that traditional threshold-based monitoring systems would almost certainly miss. Deep learning models are now being trained to predict potential system compromises based on historical patterns and emerging threat intelligence, moving the needle from detection to true prevention. This synergy allows for a predictive approach to security where vulnerabilities are patched in the digital model and then deployed to the physical hardware before an exploit can ever be successfully executed by a malicious actor.
To maintain the absolute integrity of the data flowing between the physical and virtual worlds, blockchain technology provides a decentralized and tamper-resistant ledger that secures the communication backbone. This integration directly addresses the persistent risk of data corruption, creating a trustless environment where every exchange across a global supply chain is verifiable, transparent, and immutable. When a sensor sends a status update to its Digital Twin, the blockchain ensures that the information has not been intercepted or altered in transit by an adversary. Furthermore, Digital Twins are now being used to support Zero-Trust architectures by facilitating the continuous, granular authentication of every user and device within the network. In this framework, no entity is granted access to sensitive operational parameters without rigorous and ongoing verification against the digital twin’s record. This multi-layered defense strategy ensures that even if one layer is breached, the core operational logic remains shielded by a cryptographic wall.
Navigating Implementation Challenges: Data Management and Security Risks
Despite the undeniable strategic advantages, several significant technical hurdles remain for the widespread implementation of Digital Twin-enabled security, most notably the astronomical volume of data involved. Managing the massive influx of information from thousands of disparate sensors requires immense computational power and highly specialized edge storage solutions to avoid the pitfalls of network latency. If the synchronization between a physical asset and its digital replica lags by even a fraction of a second, a window of vulnerability opens that can be exploited by high-speed automated attacks. This synchronization gap can also lead to the generation of false positives, where the security system triggers an emergency response based on outdated or misaligned data. Organizations must therefore invest in high-bandwidth communication infrastructure and sophisticated data-cleansing algorithms to ensure that the virtual model remains a perfectly timed reflection of the physical reality it is designed to protect.
Furthermore, the introduction of a sophisticated Digital Twin layer paradoxically expands the total attack surface of an organization, as the virtual environment itself becomes a high-value target for hackers. If an adversary gains unauthorized access to the digital twin, they could potentially manipulate the physical system by feeding it false instructions or masking malicious activities behind a curtain of simulated normalcy. Protecting the twin requires the highest level of encryption and strict access control measures, effectively necessitating a security strategy for the security tool itself. Additionally, many established industrial facilities still rely on legacy equipment and aging controllers that lack the modern communication protocols required to interface with contemporary Digital Twin platforms. Bridging this gap often requires the development of creative middleware solutions or expensive hardware upgrades, which can represent a significant barrier to entry for smaller enterprises looking to modernize their security posture in an increasingly hostile digital landscape.
Strategic Pathways: Future Governance and Edge Computing
To navigate these complex implementation challenges, industrial leaders have increasingly turned toward edge and hybrid computing strategies that process critical data much closer to the physical source. By shifting the heavy lifting of data analysis away from centralized cloud servers and toward the edge of the network, organizations have successfully reduced latency and enabled nearly instantaneous response times for anomaly detection. The adoption of federated learning has also gained significant traction, allowing various facilities to train their security AI models across decentralized locations without ever needing to exchange sensitive raw data. This approach preserves operational privacy while simultaneously improving the collective intelligence of the security network, as the digital twins learn from a wider variety of threat signatures. These technological advancements have helped bridge the gap between theoretical cybersecurity research and the practical, high-speed requirements of real-world industrial applications.
Standardization and governance have played a defining role in the long-term success of Digital Twins as the primary defense mechanism in the Industry 5.0 era. Organizations that aligned their digital operations with international frameworks, such as the NIST Cybersecurity Framework or ISO/IEC 27001, ensured that their various platforms remained interoperable across diverse industrial sectors and global supply chains. By prioritizing scalable integration platforms and maintaining a strict focus on human-centric design, the industry made certain that Digital Twins remained an accessible and essential tool for human operators rather than a black-box system. Strategic investments in workforce training and the development of open-source communication standards paved the way for a more inclusive technological landscape. These efforts successfully transformed the industrial sector from a fragmented collection of vulnerable nodes into a unified and resilient ecosystem capable of withstanding the most sophisticated cyber challenges of the modern age.