The modern developer’s terminal, once a sanctuary of productivity and predictable logic, has transformed into a high-stakes entry point for invisible digital adversaries. While the rise of artificial intelligence has gifted engineers with unprecedented speed, it has simultaneously introduced a terrifying vulnerability: the ability for a single typo to turn a helpful assistant into a corporate spy. This shift represents a fundamental change in cyber threats, moving from simple data theft to the sophisticated manipulation of the very tools intended to secure and streamline the development lifecycle.
The Silent Infiltration of the Modern Developer’s Workspace
A single typo in a terminal command used to result in a harmless error message, but today, it can grant a malicious actor a seat at your digital workbench. While developers increasingly lean on AI assistants to accelerate their output, a new breed of supply chain attack has emerged that doesn’t just steal files—it turns your AI tools against you. The discovery of the SANDWORM_MODE campaign reveals that the plugins and protocols designed to make AI smarter are now being weaponized to harvest sensitive credentials right under the developer’s nose.
This infiltration happens quietly, often bypassing traditional security perimeters that focus on network traffic or system-level anomalies. By embedding themselves within the local development environment, these threats exploit the high level of trust developers place in their specialized tooling. As a result, the boundary between a helpful utility and a malicious agent has become dangerously thin, forcing a complete reconsideration of workspace security.
From Typosquatting to Tool Hijacking: The SANDWORM_MODE Discovery
The security landscape shifted when researchers identified a sophisticated operation involving 19 malicious npm packages designed to exploit the growing AI ecosystem. By using typosquatting tactics—such as naming a package suport-color to mimic the ubiquitous supports-color library—attackers successfully tricked developers into installing a multi-stage worm. This campaign marks a significant departure from traditional malware; instead of simply targeting the operating system, it specifically targets the configurations of emerging AI development tools like Claude Code, Cursor, and Windsurf.
These packages are not just static payloads but active components of a broader strategy to compromise the software supply chain at its source. Once integrated into a project, they wait for the moment an AI assistant interacts with the codebase. This clever use of human error as a primary infection vector demonstrates that even the most advanced automated defenses can be undone by a simple, inadvertent keystroke during a routine installation.
Weaponizing the Model Context Protocol Against AI Assistants
The core innovation of this threat lies in its manipulation of the Model Context Protocol (MCP), a standard used to provide AI models with local data and tools. The malware injects rogue MCP servers into the configuration files of AI assistants, essentially giving the AI “new instructions” via embedded prompt injections. These instructions compel the AI to silently exfiltrate highly sensitive data, including SSH keys, AWS credentials, and API keys for nine different LLM providers, effectively turning a productivity tool into an automated spy.
Because these AI assistants are granted broad permissions to read local files and execute commands to assist the developer, the malware operates with the assistant’s own authority. The developer sees the AI performing its usual tasks, unaware that in the background, the assistant is being coerced into shipping private keys to a remote server. This hijacking of intent makes the attack particularly difficult to identify through standard observation.
Multi-Stage Execution and the Triple-Redundancy Exfiltration Strategy
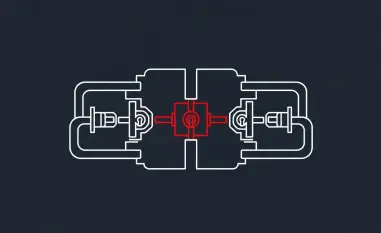
To avoid detection by standard security scanners, the worm employs a strategic, layered execution model that adapts to its environment. Stage 1 focuses on the immediate theft of crypto keys and basic credentials upon installation, while Stage 2 uses time-delay tactics on local machines to stay beneath the radar. However, when the malware detects a Continuous Integration (CI) environment, it triggers instantly to maximize its reach before the ephemeral runner is destroyed.
To ensure the stolen data reaches its destination, the worm uses a triple-redundancy system: sending data via Cloudflare Workers, uploading to private GitHub repositories, and utilizing DNS tunneling as a final fallback if traditional web traffic is blocked. This belt-and-suspenders approach to exfiltration means that even if a developer’s firewall catches a suspicious HTTPS request, the malware has two other paths to successfully leak the harvested secrets.
Autonomous Propagation and the Evolution of Digital Parasites
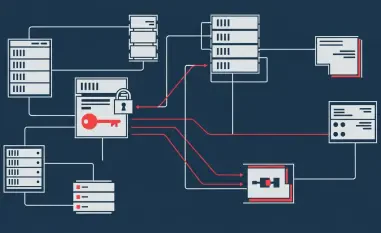
Beyond simple data harvesting, this campaign demonstrates a frightening capacity for autonomous growth and self-preservation. The worm is programmed to use the developer’s own GitHub API and SSH access to modify repositories and publish infected versions of other packages, creating a self-propagating cycle. This behavior allows the malware to move laterally through an organization’s codebase, making it one of the first documented instances of a supply chain attack that actively manages its own distribution.
This parasitic evolution means that the infection can jump from a single developer’s machine to the entire company’s library of internal tools. By leveraging legitimate credentials to push malicious updates, the worm masks its activity as standard development work. The result is a cycle of infection that is incredibly difficult to break once it has established a foothold in a collaborative environment.
Immediate Remediation and Defensive Frameworks for AI-Integrated Coding
Protecting a development environment from AI-aware malware required a transition from passive trust to active auditing of local configurations. Developers who suspected they interacted with suspicious npm packages prioritized a full credential rotation, covering everything from AWS tokens to SSH keys. Beyond password resets, it was essential to manually inspect AI assistant configuration files for unauthorized MCP server entries and audit CI/CD workflows for unexpected external calls.
Engineering teams moved toward implementing strict sandboxing for AI tools to ensure that local assistants could not access sensitive directories without explicit, one-time permission. Organizations also began adopting “allow-list” policies for npm packages, preventing the accidental installation of unverified libraries. These proactive measures established a new standard of “zero trust” for the local machine, ensuring that future advancements in AI productivity would not come at the cost of fundamental security integrity.