Malik Haidar is a veteran cybersecurity expert who has spent years navigating the complex digital defenses of multinational corporations. With a background that seamlessly blends deep technical analytics with strategic business intelligence, he specializes in identifying how emerging technologies can be weaponized by adversaries. His recent work has focused heavily on the democratization of cybercrime, specifically how artificial intelligence allows actors with minimal technical backgrounds to achieve the operational scale once reserved for nation-state groups. In this discussion, we explore the mechanics of a massive breach involving over 600 firewall instances and what it reveals about the shifting nature of global digital threats.
An individual with limited technical skill can now compromise over 600 firewall instances globally by using generative AI for reconnaissance and coding. How does this shift the traditional threat landscape, and what specific steps should security teams take to counter this massive increase in operational scale?
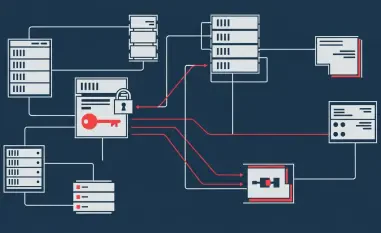
This shift fundamentally breaks the old “barrier to entry” that once kept amateur actors from causing widespread damage. In this specific campaign, we saw a single Russian-speaking actor exploit 600 FortiGate instances across 55 different countries, a feat that traditionally would have required a large, highly coordinated team of specialists. By using GenAI to generate step-by-step exploitation instructions and prioritize tasks, a lone wolf can now function like a mid-sized enterprise. Security teams must respond by moving away from reactive patching and focusing on aggressive external surface management. You have to assume that if an interface is visible, it is already being scanned by an AI-driven bot; therefore, the first step is ensuring management ports are completely disconnected from the public internet.
Many large-scale compromises bypass sophisticated exploits entirely, instead targeting exposed management ports and single-factor authentication. Why do these fundamental security gaps persist in enterprise deployments, and how can organizations better automate the detection of these misconfigurations across global networks?
These gaps persist because many organizations prioritize rapid deployment and ease of remote access over rigorous security hardening, often leaving ports like 443, 8443, or 10443 wide open for convenience. In this case, the attacker didn’t need a “zero-day” exploit because the front door was essentially unlocked with a common key. To combat this, organizations need to implement automated “outside-in” scanning that mimics an attacker’s perspective to flag any management interface that shouldn’t be reachable. We need to treat a single-factor authentication login on a firewall as a critical failure event, triggering an automated workflow that isolates the device until multi-factor authentication is enforced.
Using AI to generate prioritized task trees and Python scripts for decrypting stolen configurations represents a highly organized workflow. In what ways are these AI-driven methodologies changing the speed of lateral movement, and what specific metrics should defenders monitor to identify this automated behavior?
The speed of lateral movement is accelerating because the decision-making process is being offloaded to AI, allowing the attacker to parse, decrypt, and organize stolen configuration files in seconds. Once they have these files, they understand the entire network topology and firewall policies, which allows them to glide through the environment with surgical precision. Defenders need to monitor for “DCSync” operations and the creation of new scheduled tasks that mimic legitimate Windows services, as these are often the fingerprints of an automated script working through a network. When you see an account name designed to “blend in” appearing across multiple segments in a matter of minutes, that’s a clear indicator of an AI-augmented workflow rather than a human operator manually typing commands.
Threat actors are increasingly targeting backup infrastructure to destroy recovery capabilities before deploying ransomware. Beyond simply rotating credentials, what architectural changes are necessary to isolate backup servers, and how can teams verify that their recovery systems remain untampered during a silent breach?
In this campaign, the attacker specifically targeted Veeam Backup & Replication servers because they knew that compromising the backup infrastructure effectively removes the victim’s “get out of jail free” card. To prevent this, backup servers must be placed in a strictly isolated management zone that requires hardware-based MFA and has no direct path from the general user network. We also need to implement “immutable” backups that cannot be deleted or modified for a set period, even with admin credentials. Verification should involve regular, automated “heartbeat” checks of the backup store’s integrity and monitoring for any unauthorized access to credential stores, ensuring that the safety net hasn’t been cut before the ransomware is ever triggered.
Restricting management interfaces to known IP ranges and implementing multi-factor authentication are critical defenses against AI-augmented “spray and pray” attacks. What are the most common hurdles to implementing these changes across hundreds of locations, and how do you recommend auditing VPN logs for geographic anomalies?
The biggest hurdles are often the sheer logistical complexity of managing hundreds of disparate locations and the fear of locking out legitimate admins who may be connecting from dynamic or remote IPs. However, the “spray and pray” methodology used in this breach—targeting 600 devices—succeeds specifically because these hurdles lead to procrastination in security updates. I recommend a centralized logging strategy where VPN connection logs are analyzed in real-time for geographic “impossible travel” or logins from unexpected countries. If your company doesn’t have operations in South Asia or Northern Europe, yet you see a successful login from those regions, the system should automatically terminate the session and rotate the SSL-VPN credentials.
What is your forecast for AI-driven cyberattacks?
I believe we are entering an era of “automated persistence” where attackers will no longer need to spend weeks manually probing a target; instead, they will deploy AI agents that can adapt to defensive measures in real-time. We will see a massive surge in financially motivated “amateur” groups who use these tools to perform high-level tasks like custom malware coding and complex data parsing that were previously the domain of state-sponsored APTs. The sheer volume of attacks will likely overwhelm teams that still rely on manual verification, making AI-driven defense an absolute necessity rather than a luxury. Ultimately, the future of cybersecurity will be a battle of “AI versus AI,” where the winner is determined by who has the better-trained models and the most robust fundamental security hygiene.