The digital trust that underpins the global software ecosystem is under siege as threat actors shift from targeting individual companies toward poisoning the very tools used to secure them. This paradigm shift represents a fundamental transformation in cyber warfare, where the defensive perimeter is no longer just breached but effectively turned against itself. When the software meant to verify the safety of a codebase becomes the delivery mechanism for a backdoor, the foundational assumptions of enterprise security begin to crumble.
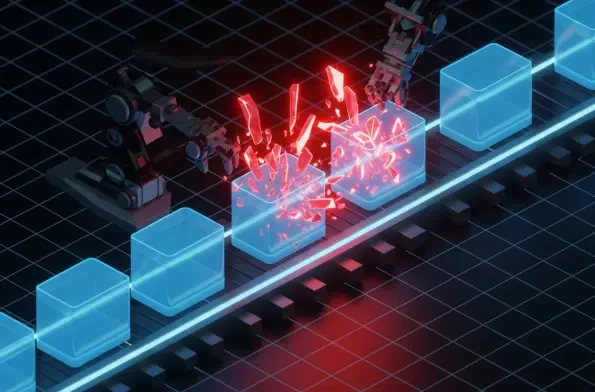
Recent breaches involving high-leverage tools demonstrate a frightening evolution in offensive tactics, where a single vulnerability in a continuous integration and continuous delivery (CI/CD) pipeline can cascade into a massive, multi-ecosystem compromise. The speed at which these infections spread suggests that modern infrastructure is more fragile than previously estimated. This article analyzes the rise of interconnected supply chain attacks, examining the TeamPCP campaign as a primary case study to explore the future of software integrity in a world of snowballing breaches.
The Anatomy of the TeamPCP Campaign: Growth and Escalation
Data and Growth Trends: Expanding the Attack Surface
The TeamPCP campaign has executed a masterclass in ecosystem expansion, successfully infiltrating five distinct environments including GitHub Actions, Docker Hub, npm, Open VSX, and PyPI. This multi-pronged approach demonstrates that modern attackers are no longer content with localized successes; they seek to maximize their reach by hitting the shared repositories that developers rely on daily. By embedding malicious code within these hubs, the threat actors ensure their payloads reach thousands of downstream targets simultaneously.
The statistical significance of these attacks is underscored by the widespread adoption of AI and security tools. For instance, LiteLLM, a library recently compromised by this group, is reportedly present in 36% of cloud environments. This high density of installation creates a target-rich environment where a single exploit can grant access to a vast portion of the global digital infrastructure. The velocity of infection has also accelerated, with data showing a rapid transition from the initial compromise of a CI/CD tool to downstream production impacts within just a few days.
Case Study: The LiteLLM and Trivy Compromise
The specific mechanics of the LiteLLM compromise reveal a sophisticated chain of infection that began with the Trivy security scanner. By compromising the scanner itself, attackers were able to inject malicious code into LiteLLM versions 1.82.7 and 1.82.8. This irony is not lost on the security community; a tool designed to find vulnerabilities became the primary vector for introducing them. This maneuver bypassed traditional perimeter defenses that typically trust security-oriented software without additional scrutiny.
The technical breakdown of this event involves a three-stage payload designed for maximum impact. Initially, the malware performs a comprehensive credential harvest, sweeping for SSH keys, Kubernetes secrets, and cloud credentials. This is followed by a lateral movement phase where the attacker attempts to gain control over Kubernetes clusters. Finally, the malware installs a persistent systemd backdoor that polls a remote server for additional instructions, ensuring that the attackers maintain a foothold even if the initial malicious package is removed.
Automated Execution Tactics: The Rise of Aggressive Launchers
To ensure the highest possible infection rate, the group employed a more aggressive .pth launcher technique in version 1.82.8 of the library. This method leverages the way the Python interpreter processes configuration files during startup, triggering the malicious logic on every Python process within the environment. This occurs without any direct user interaction or the need to import the library, making it an exceptionally stealthy and effective persistence mechanism.
Industry Perspectives: Addressing Systemic Fragility
Expert Insights: The Feedback Loop of Failure
Industry experts have highlighted a dangerous feedback loop where compromised security tools provide the credentials necessary to breach the next high-value target. Gal Nagli from Wiz noted that this creates a cycle of failure that is difficult to break once initiated. When a CI/CD runner is compromised, the attacker gains access to secrets that allow them to push malicious updates to other repositories, which in turn infects the developers who download those updates.
Furthermore, observations from Socket and Endor Labs suggest a deliberate pivot in TeamPCP’s strategy. The group has moved from simply disrupting developer environments to actively targeting production Kubernetes clusters. This shift signifies a move toward high-leverage points in the software stack, allowing attackers to maximize their “blast radius.” By focusing on the infrastructure that orchestrates modern applications, they can exert control over the entire operational lifecycle of an enterprise.
Convergence: Supply Chain Attacks and Extortion
A particularly alarming development is the apparent collaboration between supply chain threat actors and high-profile extortion groups. Analysis suggests that TeamPCP may be coordinating with entities similar to the LAPSUS$ group to monetize the data stolen during these campaigns. This partnership combines the technical finesse required for supply chain infiltration with the aggressive negotiation and pressure tactics used in large-scale data theft and extortion.
The motivation behind these attacks appears to be both financial and ideological. In public statements, the actors have mocked the current state of security research, labeling it a “joke” and expressing an intent to exfiltrate terabytes of trade secrets. This rhetoric indicates that the attackers are not merely looking for a quick payout but are committed to a long-term campaign of disruption and intellectual property theft, viewing the software supply chain as a wide-open door.
The Future of Software Integrity: Risk and Mitigation
Predicted Developments: Weaponizing the Defensive Stack
Looking forward, the trend of weaponizing security tooling is expected to intensify. Scanners, CI/CD runners, and linters will likely become the primary delivery vehicles for malware because they inherently possess the high-level permissions required to move throughout a network. Organizations must prepare for a future where their most trusted applications are the ones most likely to be turned against them.
Additionally, the rise of AI-native risks presents a unique challenge for the coming years. As specialized libraries like LiteLLM become essential components of enterprise infrastructure, they introduce new vulnerabilities that traditional security models are ill-equipped to handle. The complexity of the modern AI stack, combined with the deep integration required within Kubernetes and container orchestration layers, provides attackers with ample opportunities to hide persistent backdoors.
Necessary Defensive Shifts: Moving Toward Zero Trust
To counter these evolving threats, the industry must move beyond simple detection and adopt a model of comprehensive identity auditing. This involves the immediate rotation of all non-human identities and machine credentials following any suspected breach. Static secrets are no longer viable in an era where automated harvesting can compromise an entire environment in minutes. Transitioning to short-lived, dynamically generated credentials will be essential for limiting the damage of a supply chain compromise.
Moreover, the “Zero Trust” philosophy must be extended to the software supply chain itself. Third-party dependencies can no longer be treated as inherently safe. Defensive strategies will need to incorporate runtime monitoring and strict egress filtering to ensure that compromised packages cannot communicate with external command-and-control servers. By treating every piece of code as potentially malicious, organizations can build more resilient systems that survive even when the tools they rely on are compromised.
Conclusion: Securing the New Digital Frontier
The escalation of supply chain attacks shifted the landscape from isolated incidents to systemic campaigns that leveraged the interconnected nature of modern software. This transition demonstrated that the speed and scale of digital adoption had outpaced the defensive measures intended to protect it. The TeamPCP incident served as a stark reminder that security tool sprawl created more vulnerabilities than it solved, especially when those tools were not themselves fortified against sophisticated interference.
To move forward, organizations had to prioritize active defense over static patching, recognizing that the lifecycle of a CI/CD pipeline required constant auditing. The focus turned toward the rotation of environment secrets and the implementation of more granular access controls for non-human entities. By acknowledging the fragility of the software ecosystem, the industry began the difficult work of rebuilding digital trust on a foundation of verification rather than assumption. This shift was necessary to break the cycle of escalation and secure the future of global enterprise infrastructure.