Hackers & Threats
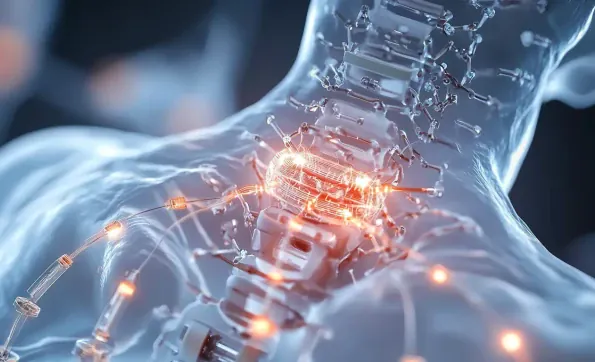
The development of wireless medical implants has revolutionized patient care, providing capabilities for remote monitoring and treatment adjustments that were previously impossible. Engineers at Rice University have responded to the challenge of securing these advanced devices, developing a robust
The Singapore Armed Forces (SAF) has taken a significant step to enhance national cyber defense with the official launch of two new cyber commands on March 18. This strategic initiative aims to tackle the rising sophistication and frequency of cyber threats, ensuring Singapore's digital

The wave of Distributed Denial of Service (DDoS) attacks sweeping across Europe highlights a pressing need for advanced cybersecurity measures. In fact, the European Cyber Report 2025 reveals a staggering 137% surge in DDoS attacks on the Link11 network over the past year. These attacks are not

In today's digital age, cybersecurity is more critical than ever, with organizations facing a relentless wave of cyber threats. The need for robust systems and proactive measures for threat detection and analysis cannot be overstated, as the cost of data breaches and cyberattacks continues to

The ubiquitous nature of apps in today's digital age has brought not just unparalleled convenience but also significant risks, as seen with the alarming rise in spyware within the Google Play Store. The Google Play Store, relied upon daily by millions globally, is facing increasing incidents

In a startling sequence of events that has raised alarms globally, Elon Musk's social media platform, X, was hit by a significant cyberattack that rendered it partly unusable for several hours. The disruption was a result of a distributed denial-of-service (DDOS) attack that Musk claims