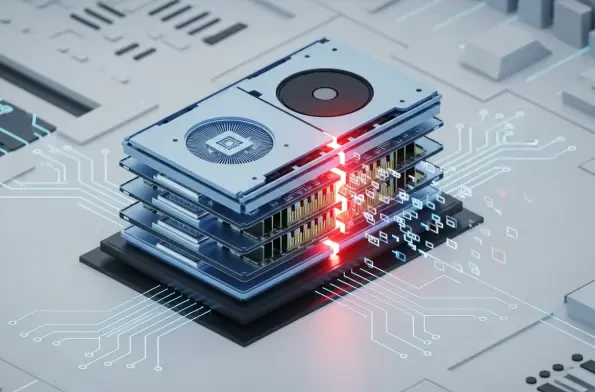
The historical boundary separating peripheral hardware from core system authority has dissolved as researchers demonstrate that high-performance graphics processors can be coerced into betraying their host systems through silicon-level manipulations. This transformation, catalyzed by the GPUBreach vulnerability, signifies a pivot from localized data corruption toward systemic takeover. In the contemporary technological landscape, GPUs are no longer merely auxiliary accelerators; they are central to the compute fabric of artificial intelligence and high-performance computing. Consequently, a breach at this level does not just threaten a single application but compromises the entire architectural trust model of modern servers.
Introduction to GPU Memory Vulnerabilities
Hardware vulnerabilities typically focus on the central processor, yet the sheer complexity of modern graphics units has introduced a sprawling attack surface. As memory density increases to meet the demands of generative AI, the physical proximity of transistors leads to unintended electrical interactions. GPUBreach emerges as a sophisticated exploit family that weaponizes these interactions, shifting the RowHammer threat into the high-bandwidth domain. This evolution reflects a broader trend where attackers target specialized hardware components that lack the decades-long security hardening applied to CPUs.
This vulnerability functions by exploiting the physical properties of Dynamic Random-Access Memory (DRAM). Because the GPU is integrated so deeply into the system memory management, any instability in its dedicated RAM can have cascading effects on the host. This matters because the industry has traditionally assumed that GPU memory is isolated from the sensitive kernel space of the CPU. The emergence of GPUBreach proves this assumption is no longer valid, necessitating a complete re-evaluation of how hardware boundaries are defined in high-performance systems.
The Architecture of GDDR6 RowHammer Exploits
GDDR6 Memory Susceptibility and Bit-Flipping
GDDR6 memory, the backbone of modern graphics cards, achieves its massive throughput through extreme physical density, which inadvertently makes it fertile ground for bit-flipping. By repeatedly accessing specific memory addresses at high frequencies, an attacker can induce a charge leak that flips a binary value in a neighboring, unaccessed cell. This is not a software bug but a physical limitation of the hardware itself. The significance lies in the fact that these flips occur within the high-speed environment of the GPU, which was previously thought to be too noisy or complex for such precise manipulation.
The unique aspect of this implementation is its ability to bypass the internal noise and timing protections inherent in graphics architectures. Unlike standard desktop RAM, GDDR6 operates with much higher clock speeds and different refresh cycles. However, the researchers discovered that these very features could be leveraged to increase the success rate of a bit-flip. This vulnerability exposes a critical flaw in the hardware supply chain where performance gains have outpaced the physical stability of the memory modules themselves.
GPU Page Table Manipulation
The true danger of GPUBreach manifests through the strategic corruption of GPU page tables, which manage how the hardware translates virtual addresses into physical memory locations. By flipping specific bits within these translation entries, an attacker can trick the GPU into accessing memory regions it should not even see. Unlike traditional exploits that target application data, this method subverts the very map the hardware uses to navigate, granting the graphics processor “god-mode” access to its own memory space and, eventually, the host system memory.
This technique is particularly devastating because it bridges the gap between the isolated GPU environment and the host operating system. By manipulating these tables, a compromised process can bypass Input-Output Memory Management Unit (IOMMU) protections that were designed specifically to prevent this kind of unauthorized access. It is this specific ability to render hardware-level isolation useless that makes GPUBreach a superior threat compared to older, software-reliant exploits.
Evolution of Parallel Hammering Techniques
Previous RowHammer attempts were often stifled by the architectural barriers of GPU schedulers, yet the transition toward parallel hammering has changed the calculus. Modern exploits utilize the thousands of cores available on a GPU to perform synchronized, high-frequency hammering patterns. This innovation overcomes the randomness of standard memory access, ensuring that the electrical stress is concentrated enough to force a bit-flip. This shift in behavior indicates that as hardware becomes more parallel, the potential for coordinated hardware attacks grows exponentially.
Moreover, these parallel techniques have evolved to become more stealthy, evading detection by standard performance monitoring tools. By distributing the hammering workload across numerous threads, the attack avoids the thermal spikes or latency issues that would typically trigger an alarm. This sophisticated coordination reflects a broader trend in the cybersecurity landscape where attackers are using the core strengths of the hardware—its massive parallelism—against the security of the system itself.
Real-World Applications and Attack Scenarios
The implications are most severe in multi-tenant cloud environments where a single physical GPU is partitioned among various users. If a malicious actor can trigger a bit-flip that escalates privileges, the isolation between different virtual instances vanishes. Notable implementations of this attack have demonstrated the ability to leak cryptographic keys from sensitive libraries or significantly degrade the accuracy of large-scale machine learning models. This transforms a technical hardware glitch into a practical tool for industrial espionage in the world’s most critical data centers.
Furthermore, the rise of edge computing means that even consumer-grade devices are at risk. In these scenarios, the GPU is often the most accessible component for an attacker via WebGPU or other browser-based APIs. By running a malicious script in a browser tab, an attacker could theoretically trigger a bit-flip that compromises the entire device, from the operating system to stored credentials. This democratization of high-level exploits means that security can no longer be guaranteed by simply restricting physical access to the server room.
Challenges in Hardware Mitigation and Driver Security
Mitigating these hardware-level threats remains an uphill battle due to the fundamental nature of DRAM physics and the limitations of current drivers. Error-Correcting Code (ECC) memory is often cited as a defense, but it is not a panacea; it can be overwhelmed by multi-bit flips that exceed its correction capacity. Furthermore, software-level mitigations often introduce massive performance overheads that negate the very reason for using a GPU in the first place. The industry faces a paradox where securing the hardware may require throttling the performance that makes it valuable.
Regulatory issues also complicate the path forward, as standardizing hardware security requires cooperation across global semiconductor manufacturers. While some companies have attempted to implement Target Row Refresh (TRR) as a countermeasure, researchers have consistently found ways to circumvent these protections. This cat-and-mouse game highlights a deep-seated vulnerability in the global hardware infrastructure that cannot be solved with a simple software patch or a single firmware update.
Future Outlook for GPU Isolation and Security
Looking forward, the focus must shift from reactive patching toward security-by-design for GPU architectures and their respective drivers. We are likely to see a movement toward more robust hardware isolation techniques and perhaps new memory technologies that are physically immune to electrical leakage. The long-term impact will be a redefinition of the trusted computing base, where the GPU is treated with the same skepticism and rigorous isolation as a network interface, rather than a trusted internal component.
Additionally, we may see the emergence of AI-driven security monitors that can detect the specific memory access patterns associated with RowHammer in real-time. These systems could theoretically interrupt a hammering process before it successfully flips a bit, providing a dynamic defense that adapts to new attack vectors. However, the success of such technologies will depend on their ability to operate without significantly impacting the computational throughput that industries rely on for large-scale data processing.
Summary and Assessment
The GPUBreach vulnerability provided a stark reminder that physical hardware limitations can be weaponized with surgical precision to bypass sophisticated software defenses. By bridging the gap between GPU memory instability and CPU kernel compromise, this exploit redefined the scope of what constitutes a system-wide threat. The industry recognized that the drive for higher memory density must be balanced with architectural resilience, as the cost of a hardware-level breach proved too high for the growing AI infrastructure to ignore.
Ultimately, the assessment of this technology’s current state showed a critical need for a paradigm shift in how peripherals are integrated into secure systems. While the performance of GDDR6 remained unparalleled, its security trade-offs created a vulnerability that could not be ignored by cloud providers or security researchers. Moving forward, the lessons learned from GPUBreach set a new standard for hardware validation, ensuring that future generations of high-performance computing are built on a foundation that is as secure as it is fast.