Editorial
The ransomware playbook has changed. Encryption is no longer the main pain point; stolen data is. Criminal groups are monetizing breaches twice: first by locking systems, then by threatening to publish or sell confidential information. That pressure campaign works because the business fallout is

The rapid integration of sophisticated artificial intelligence and interconnected supply chains has fundamentally altered the vulnerability profile of the modern enterprise, rendering traditional perimeter-based security models obsolete in the face of state-sponsored hybrid threats. As of early

Your network may already be compromised, and your security tools could have missed this. Attackers are slipping through protective measures undetected, exploiting trusted processes, and hiding in plain sight. Signature-based antivirus and basic firewalls, once the cornerstones of digital defense,
The projected annual cost of cybercrime is $10.5 tillion . As attacks grow in scale and cost, there’s more pressure on businesses to protect themselves. Meaning, cybersecurity isn’t just an IT problem, but it’s a leadership concern. Many catastrophic cyber incidents result from leadership blind spot

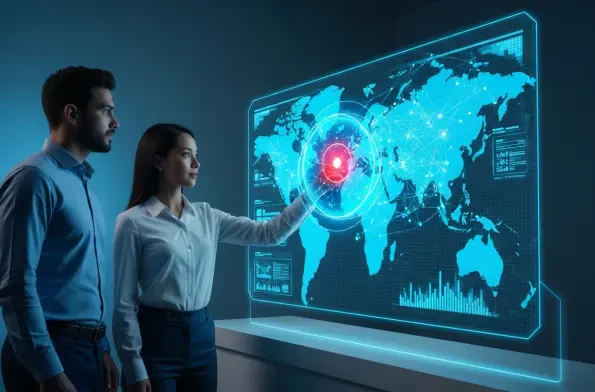
Cybersecurity is ultimately about trust. While technical defenses play a key role, it’s how an organization responds that protects its reputation and financial well-being. With ransomware incidents up 25%, data breaches increasing by 43% , and the underground market growing more resilient, t

In 2025, cyber threats from nation-states have become more active, aggressive, and advanced. Unlike regular cybercriminals, these state-sponsored actors often have long-term goals. They aim to steal valuable intellectual property, gather intelligence for political or military reasons, and influence