Malik Haidar is a seasoned cybersecurity expert who has spent years bridging the gap between deep technical defense and high-level corporate strategy. Having managed complex security landscapes for multinational corporations, he specializes in transforming raw threat intelligence and operational data into actionable business insights. His approach moves beyond simply stopping hackers; he focuses on how security investments protect a company’s bottom line and drive long-term enterprise value. In this discussion, he explores why the traditional language of “vulnerability scores” is failing in the boardroom and how financial modeling is becoming the new standard for modern security leadership.
Traditional dashboards focus on vulnerability scores and patch rates. How do these operational metrics fall short during budget season, and what specific financial indicators should security leaders prioritize to align with board-level enterprise risk management?
Operational metrics like vulnerability counts and severity scores are excellent for the “engine room” of security, but they fall flat in the boardroom because they describe activity rather than economic impact. When budget season arrives, an executive doesn’t necessarily care that you improved detection coverage by 22%; they want to know how that reduction in technical debt translates to reduced financial exposure. To align with enterprise risk management, security leaders should prioritize indicators like Annual Loss Expectancy (ALE), cost avoidance, and net present value. By focusing on downside exposure and capital efficiency, you shift the narrative from a technical “to-do list” to a strategic discussion about protecting the organization’s profit margins. This financial clarity turns cybersecurity from an opaque cost center into a measurable risk-reduction investment that the CFO can actually get behind.
Annual Loss Expectancy (ALE) uses likelihood and impact assumptions to value cyber risk in dollar terms. How do you construct these scenarios for a board meeting, and what role do variables like infrastructure footprint and regional data play in creating a credible estimate?
Constructing a credible ALE scenario begins by moving away from guesswork and toward a structured four-step framework. First, we identify a realistic threat scenario, such as a ransomware attack, and use organizational inputs like employee count and infrastructure footprint to ground the data in reality. Regional variables are critical here because the cost of a data breach in the U.S. differs significantly from one in Europe due to varying regulatory fines and recovery costs. We then combine the likelihood of the event occurring with the total potential financial impact, including operational downtime and reputational damage. This step-by-step approach allows us to present a dollar-based risk profile that feels specific to our company’s unique geography and scale.
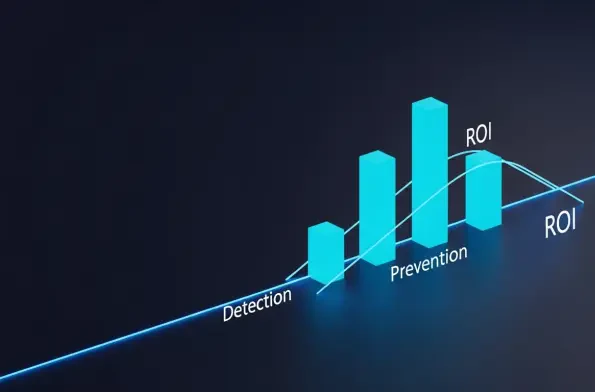
Detection metrics track performance after an attack begins, while prevention controls aim to shift the probability of success. How does this distinction change an organization’s expected loss curve, and what financial outcomes are most impacted when a company prioritizes outcome-based modeling?
The distinction between detection and prevention is the difference between managing an ongoing crisis and avoiding one altogether. Detection and response metrics measure how well we perform after a breach has already started, which is vital but essentially reactive. Prevention controls are different because they fundamentally change the probability of an attack succeeding, which shifts the entire expected loss curve downward. When we prioritize outcome-based modeling, the financial outcomes most impacted are the frequency of breaches and the total exposure to recovery costs. Essentially, while detection measures events that are already costing us money, prevention changes the financial outcome by ensuring those costs never hit the ledger in the first place.
Justifying a security budget requires aligning investments with measurable risk reduction. Can you walk through the process of modeling prevention impact and estimating ROI, and how does this shift the conversation from a technical “cost center” to a value-driven discipline?
To model prevention impact, we start by comparing our current financial exposure to a projected “post-investment” state where specific controls are implemented. We estimate how much the investment reduces the probability of a successful exploit and then calculate the avoided breach costs across various scenarios. To make this a value-driven discipline, we must include “no-breach” scenarios where the value is derived from operational savings and the maintenance of business continuity. This allows us to show a clear Return on Investment (ROI) by demonstrating that the cost of the security tool is significantly lower than the modeled financial loss it prevents. When you can say, “We reduced modeled breach exposure by X dollars,” you are no longer asking for a handout; you are presenting a business case for capital efficiency.
Modern modeling tools allow for fast, scenario-based value estimates using a small set of organizational inputs. How should a security team integrate these tools into their quarterly reporting, and what are the potential pitfalls of relying solely on manual financial analysis?
Security teams should integrate these modern modeling tools into their quarterly reporting to provide a consistent “financial heartbeat” for the program. By using standardized inputs like infrastructure scale and regional data, teams can generate rapid, defensible estimates that track risk reduction over time. Relying solely on manual financial analysis is a major pitfall because it is often too slow, complex, and prone to human error to keep up with the fast-paced threat landscape. Furthermore, manual modeling often lacks the agility needed for effective vendor evaluation, whereas automated tools let us quickly see which technology provides the best “bang for the buck” in reducing risk. This shift to automated modeling ensures that the security team remains agile and that their reporting is always grounded in the most current business realities.
What is your forecast for the future of cyber risk quantification as AI-assisted threats and faster exploit cycles continue to increase the potential financial downside of security incidents?
My forecast is that cyber risk quantification will move from being a “nice-to-have” exercise to a mandatory leadership requirement for every CISO. As AI-assisted malware and faster exploit cycles shrink the window of opportunity for defenders, the potential financial downside of an incident is ballooning, making the cost of “getting it wrong” higher than ever. Organizations will stop accepting activity-based reporting and will instead demand real-time financial models that quantify the value of every single control in the stack. We will see a consolidation of tools as companies use these financial models to prune underperforming tech and reinvest in prevention-first strategies. Ultimately, the gap between technical security and financial management will close, and the most successful security leaders will be those who can speak the language of the board as fluently as the language of the SOC.