The rapid emergence of the cybercriminal syndicate known as The Gentlemen serves as a stark reminder that the modern ransomware landscape is defined by its volatile organizational structures and the constant recycling of high-level technical expertise. While many established threat actors struggle to maintain cohesion under increased global pressure, this group effectively leveraged a messy divorce within the Qilin ecosystem to carve out a dominant position in the underground economy. The transition from being a mere affiliate to becoming a primary Ransomware-as-a-Service provider was accelerated by the public fallout involving an operative known as “hastalamuerte,” whose internal leaks provided a rare glimpse into the group’s inner workings. This transition highlights a broader trend where seasoned developers no longer wait years to establish a brand; they instead seize pre-existing infrastructure and operational playbooks to launch massive campaigns. By adopting a dual-extortion model that focuses on both encryption and the threat of public data exposure, the group ensures that victims face extreme pressure regardless of their backup recovery capabilities or disaster response readiness.
Multi-Platform Targeting and Initial Entry
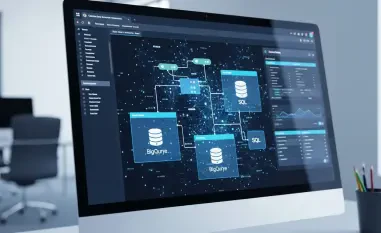
The technical sophistication of The Gentlemen is particularly evident in their ability to compromise diverse enterprise environments, ranging from traditional Windows workstations to critical Linux servers and virtualized ESXi clusters. This cross-platform capability ensures that no corner of a modern corporate network remains safe from their reach, forcing IT security teams to defend against a highly adaptable adversary that understands how to pivot between different operating systems. Their primary vector for gaining a foothold involves the aggressive exploitation of exposed FortiGate VPN devices, utilizing either known vulnerabilities that remain unpatched in many sectors or sophisticated brute-force attacks against weak credentials. Once inside the perimeter, the threat actors do not waste time; they immediately deploy automated scripts designed to harvest credentials and map the network topology. This systematic approach allows them to identify high-value targets within minutes of the initial breach, ensuring that their subsequent movements are both efficient and highly targeted toward the most sensitive data.
Building on this initial foothold, the group relies heavily on native administrative tools like Windows Management Instrumentation and PowerShell to conduct lateral movement without raising immediate alarms. By using these legitimate features, they can bypass many signature-based detection systems that are often tuned to look for overtly malicious software rather than the abuse of built-in system utilities. This “living off the land” strategy is complemented by the deployment of specialized toolkits that automate the discovery of shared drives and cloud-integrated storage solutions. As they migrate through the network, the attackers prioritize the identification of domain controllers and backup servers, which are essential for maintaining control and ensuring the victim cannot easily recover. The speed at which they transition from a single compromised endpoint to full administrative control over the entire domain is a testament to their refined operational playbooks. This efficiency reduces the window of opportunity for security operations centers to intervene before the final payload deployment begins, making rapid detection and automated response protocols more critical than ever.
Advanced Evasion and Internal Risk Factors
To maintain persistence and hinder forensic analysis, The Gentlemen employ a sophisticated “Bring Your Own Vulnerable Driver” technique that allows them to disable security software at the kernel level. By loading a legitimate but vulnerable third-party driver, the attackers can gain high-privilege access to the operating system, which they then use to terminate antivirus processes and silence endpoint detection and response sensors. This method is particularly effective because it exploits the inherent trust that the operating system places in signed drivers, making it difficult for standard security tools to block the activity without risking system stability. Furthermore, the group is known for its aggressive approach to covering its tracks, which involves the systematic deletion of Windows Event Logs and the destruction of shadow copies. These actions are designed to frustrate incident responders and digital forensic experts who attempt to reconstruct the timeline of the breach. By wiping the evidence of their presence, the threat actors prolong the investigation process and increase the likelihood that the true extent of the data exfiltration remains unknown to the victim organization.
The rise of this organization illustrated how the instability of the affiliate model could inadvertently benefit the defensive community by exposing the internal mechanics of professionalized cybercrime. While the group successfully executed high-pressure extortion campaigns, the friction between its leaders and affiliates provided researchers with the specific intelligence needed to develop more robust detection signatures for their unique toolsets. For organizations looking to mitigate such risks, the most effective path forward involved the immediate hardening of edge gateway devices and the implementation of strict multi-factor authentication across all remote access points. Security teams also benefited from adopting a zero-trust architecture that limited the potential for lateral movement, thereby neutralizing the group’s reliance on administrative tool abuse. Proactive threat hunting focused on identifying unusual driver installations and unauthorized PowerShell activity proved to be a decisive factor in stopping the final encryption phase. Ultimately, the lessons learned from observing The Gentlemen emphasized that while infrastructure was easily rebuilt, the visibility gained through internal leaks allowed defenders to stay one step ahead of the next iteration of the model.