Modern enterprises frequently operate under the dangerous assumption that a migration to a major cloud ecosystem like Microsoft 365 inherently guarantees a robust and impenetrable security posture. While the underlying physical infrastructure and basic service availability are managed by the provider, a significant portion of the security responsibility remains firmly in the hands of the organizational IT departments. This shared responsibility model often contains overlooked gaps where default settings, left unadjusted, create a deceptive sense of safety that sophisticated adversaries are increasingly adept at exploiting. The reality is that the mere presence of advanced security tools does not equate to effective protection if those tools are not specifically tailored to the unique architectural nuances of the cloud environment. Relying on out-of-the-box configurations essentially leaves the front door unlocked, as these standard settings are designed for maximum compatibility and ease of use rather than the rigorous requirements of high-stakes corporate defense.
The Architecture of Invisible Vulnerabilities
Configuration Integrity and the Recovery Gap
A persistent misconception in cloud security is the belief that standard data backups are sufficient for comprehensive disaster recovery in the event of a breach. While organizations diligently store copies of documents and emails, they frequently neglect the complex architectural metadata and administrative settings that define the entire environment. If a tenant is compromised or suffers a catastrophic failure, the loss of these intricate configurations can be just as paralyzing as the loss of the data itself. Rebuilding thousands of conditional access policies, group permissions, and custom integration settings from scratch manually can extend downtime from hours to weeks. This “configuration gap” means that even if the raw data is restored, the operational framework required to access and secure that data is missing, leading to a state of functional paralysis.
Beyond the immediate loss of access, the lack of configuration backups creates a blind spot regarding “silent” changes made by attackers during a dwell period. An adversary who gains administrative access may not delete data but instead subtly alter security protocols to create persistent backdoors or weaken encryption standards. Without a documented and restorable baseline of the known-good configuration state, security teams find it nearly impossible to verify that the environment has been fully remediated after an incident. This realization is driving a shift toward treating infrastructure-as-code principles as a security necessity, where the entire tenant state is versioned and protected. By treating configurations with the same level of urgency as financial databases, organizations can ensure that their recovery strategies encompass the entire digital ecosystem, rather than just the files stored within it.
The Liability of Overexposed Administrative Access
The traditional model of administrative privileges in Microsoft 365 often relies on a “Global Administrator” role that grants sweeping permissions across every facet of the suite. This all-or-nothing approach to management creates an immense attack surface where a single compromised account can lead to a total organizational takeover. Many businesses continue to operate with an excessive number of high-level administrators, failing to implement the principle of least privilege due to the perceived complexity of more granular role-based access control. When an attacker hijacks a privileged account, they can manipulate mail flow rules to intercept sensitive communications, bypass multi-factor authentication for other users, and exfiltrate data without triggering basic security alerts. The centralization of power within a few accounts makes them the ultimate prize for state-sponsored actors and cybercriminals.
To mitigate this risk, there is an urgent need to move away from static, permanent administrative assignments toward dynamic and scoped authorization models. Sophisticated threat actors often monitor these high-value accounts for months, waiting for a moment when security vigilance might wane. If an administrator has broad access to SharePoint, Exchange, and Entra ID simultaneously, the potential “blast radius” of a breach is unrestricted. Organizations are now exploring ways to break down these monolithic roles into micro-permissions that are only activated when a specific task is required. By limiting the scope of what any single person can do at any given time, the enterprise effectively shrinks the target for attackers. This proactive reduction in administrative exposure is not merely an IT preference but a fundamental requirement for maintaining a resilient posture against lateral movement and internal threats.
Advanced Strategies for Tenant Resilience
Virtual Segmentation: A New Defense Paradigm
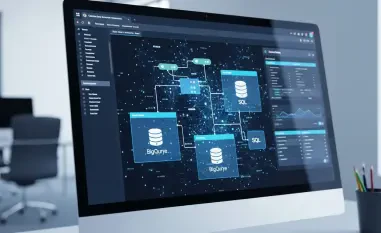
As collaboration suites become more interconnected, the concept of virtual tenant segmentation has emerged as a critical strategy for isolating sensitive workflows and limiting risk. This approach involves creating logical boundaries within a single tenant to ensure that a compromise in one department or functional area does not automatically compromise the entire organization. For instance, the financial department’s data and administrative settings can be virtually segregated from the general marketing or sales environments. This level of isolation is particularly vital for organizations that manage diverse business units or operate in highly regulated industries where data sovereignty is paramount. Virtual segmentation allows security teams to apply stricter policies to high-risk areas without impacting the productivity of the broader workforce, creating a balanced and defensible architecture.
The implementation of virtual segmentation also serves as a necessary precursor to the secure adoption of agentic AI and automated collaboration tools. In an environment where AI-driven agents perform tasks across different applications, the lack of rigid boundaries could allow an automated process to inadvertently leak confidential information from one segment to another. By enforcing strict virtual barriers, organizations can ensure that AI tools only access the data they are explicitly authorized to handle, preventing the accidental exposure of intellectual property. This strategic isolation transforms the tenant from a flat, open landscape into a series of fortified chambers. Building this architecture requires a departure from legacy management styles, favoring a more disciplined approach where access is strictly defined by the specific needs of the business unit rather than the convenience of the IT department.
Securing the Automated Future
The rapid integration of hyper-automated workflows and AI-powered assistants into Microsoft 365 introduces a new layer of complexity that traditional security playbooks are unequipped to handle. These automated systems often operate with high levels of permission to facilitate seamless data movement, but this very fluidity can be weaponized if the underlying security controls are weak. Attackers are beginning to target the logic of automated scripts and the prompts of AI agents to manipulate the system into performing unauthorized actions. Ensuring resilience in this new era requires a focus on “automation integrity,” where every automated process is subjected to the same rigorous oversight as a human user. This includes auditing the permissions of service principals and ensuring that automated tasks cannot be used to facilitate lateral movement across the cloud ecosystem.
Maintaining a secure posture in a world of autonomous digital workers necessitates a shift toward real-time behavioral monitoring and automated response. Traditional, static rules are no longer sufficient to catch an AI agent that has been subtly redirected to exfiltrate data. Security teams must employ advanced analytics to identify anomalies in how automated tools interact with sensitive datasets, ensuring that any deviation from established norms results in an immediate lockdown. The goal is to create a self-healing environment that can detect and neutralize threats at machine speed. By prioritizing the security of the automation layer, enterprises can reap the productivity benefits of modern collaboration tools without opening themselves up to the next generation of cloud-based threats. This proactive stance ensures that the digital transformation remains a source of competitive advantage rather than a significant security liability.
Strategic Directions for Enterprise Security
The evolution of cloud-based threats necessitated a radical shift in how organizations approached the security of their Microsoft 365 environments. IT leaders moved beyond the simplistic reliance on default platform safeguards, recognizing that true resilience required a deep commitment to configuration integrity and granular access control. By implementing virtual tenant segmentation, businesses effectively minimized the potential blast radius of individual breaches, ensuring that a single compromised account could no longer jeopardize the entire enterprise. Furthermore, the transition toward managing configurations as protected assets allowed for rapid, high-fidelity recovery that went far beyond basic data restoration. These advancements provided a stable foundation for the integration of agentic AI and automated workflows, allowing for innovation without the sacrifice of fundamental security principles.
Moving forward, the primary focus for security teams remained the continuous refinement of the principle of least privilege through automated authorization and real-time behavioral analysis. Organizations that succeeded in this landscape were those that treated their cloud configuration as a living, versioned architecture that required constant auditing and validation. They moved away from static security models in favor of dynamic systems capable of responding to the sophisticated tactics of modern adversaries. Ultimately, the hidden risks of the cloud were mitigated not by a single product, but by a comprehensive strategy that prioritized visibility, isolation, and the rigorous protection of administrative power. This proactive approach ensured that the digital workspace remained a secure and productive environment, capable of withstanding the complexities of an increasingly automated world.