Business Perspectives
The sanctity of personal privacy in the digital age faces constant threats from aggressive marketing tactics that deliberately circumvent established legal protections and exploit the most vulnerable members of society. In a recent enforcement action, the Information Commissioner’s Office, or ICO, i
The rapid convergence of high-speed digital networks and heavy industrial machinery has created a landscape where a single lines of malicious code can now trigger catastrophic physical consequences. While a typical data breach in a corporate office might result in leaked emails or financial loss, a

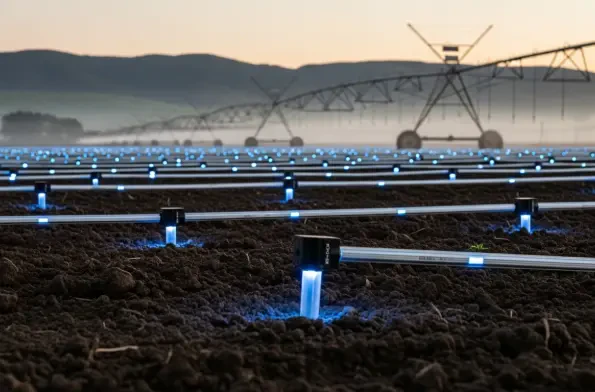
Heavy industries are currently witnessing a seismic shift as they attempt to connect millions of disparate sensors across some of the most inhospitable and geographically isolated regions on the planet, creating a demand for infrastructure that moves beyond the limitations of traditional cellular
Corporate legal departments and risk officers have long lived with the unsettling reality that nearly ninety-seven percent of their customer interactions occur in a total supervisory vacuum. This systemic oversight gap has historically forced enterprises to rely on retrospective manual audits,

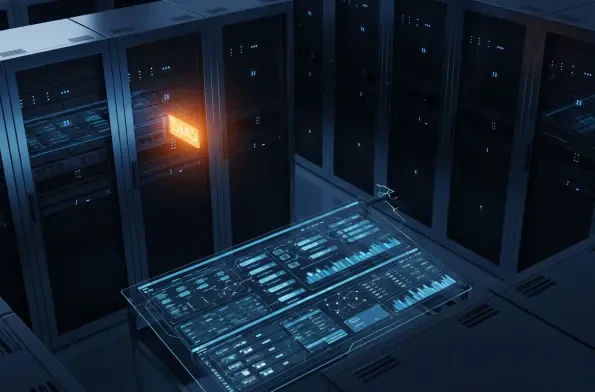
The digital landscape has transformed into a high-stakes battlefield where the distinction between a resilient enterprise and a compromised one often depends on the underlying security architecture. As we navigate the complexities of 2026, the industry remains fixated on two undisputed titans:

Modern enterprises frequently operate under the dangerous assumption that a migration to a major cloud ecosystem like Microsoft 365 inherently guarantees a robust and impenetrable security posture. While the underlying physical infrastructure and basic service availability are managed by the