Introduction
Organizations often find themselves trapped in a paradox where the pursuit of extreme scalability inadvertently opens doors to sophisticated cyber threats that legacy frameworks were never designed to handle. This strategic exploration addresses the critical balance between operational performance and digital protection, offering a roadmap for decision-makers who must navigate the complexities of modern infrastructure. Readers can expect to learn how a security-first engineering mindset transforms the cloud from a vulnerable storage environment into a hardened, resilient foundation that supports long-term growth.
The primary objective involves examining the transition from simple migration to a resilience-focused cloud design. By evaluating the gaps in traditional adoption strategies, the discussion clarifies why basic connectivity is no longer sufficient in an era of persistent atmospheric and systemic threats. The scope of this analysis covers architectural optimization, the reduction of complexity sprawl, and the essential alignment of technical investments with specific organizational missions.
Key Questions or Key Topics Section
Why Does Rapid Migration Often Lead to Increased Vulnerability?
Many enterprises feel intense pressure to abandon on-premises systems in favor of the cloud to reduce costs and increase agility. However, when the migration process prioritizes speed over structural integrity, organizations often end up with fragmented architectures that lack cohesive security boundaries. These “lift and shift” operations frequently transport old vulnerabilities into new environments where the lack of traditional perimeter controls makes them even more dangerous.
Adversaries actively look for the misconfigurations and visibility gaps that occur during these rushed transitions. Complexity acts as the primary enemy of security in these scenarios, as sprawling digital footprints become nearly impossible to monitor or defend effectively. Without a clear roadmap that accounts for the specific nuances of cloud-native threats, a tool meant to empower the business instead becomes a significant liability that invites unauthorized access and data exfiltration.
What Role Does Security-First Engineering Play in Modern Architecture?
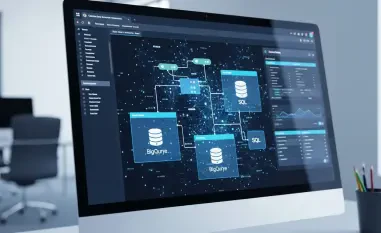
Traditional approaches often treat security as a final checkbox or a separate layer added after the infrastructure is built. In contrast, security-first engineering treats protection as a foundational requirement that is integrated into the initial design phase. This methodology ensures that every component of the cloud environment is built to withstand interference, rather than relying on reactive measures to stop an attack that has already breached the system.
Furthermore, this approach introduces the concept of continuous cyber assurance, which is a proactive strategy where security measures evolve in real-time alongside the infrastructure. By aligning cloud decisions with the core mission of the organization, stakeholders ensure that their technical footprint remains robust against shifting threat landscapes. This results in a scalable environment where performance and defense are not competing priorities but are instead mutually reinforcing characteristics.
How Can Organizations Transition From Reactive Defense to Built-In Resilience?
Moving away from a reactive posture requires a fundamental shift in how leadership views the relationship between technology and risk. Instead of deploying disparate security tools to patch holes as they appear, the focus must shift toward reducing architectural sprawl and simplifying the environment. A leaner, more organized cloud presence is inherently easier to secure because it minimizes the surface area available for potential exploitation.
Success in this transition depends on building a cohesive strategy that blends mission alignment with rigorous engineering standards. Organizations must move beyond the mentality of simply maintaining legacy systems in a new location and instead focus on optimizing their digital footprint for both defense and high-level performance. When resilience is baked into the engineering process, the cloud becomes a reliable asset capable of maintaining operational readiness even during an active cyber incident.
Summary or Recap
The examination of modern cloud strategies revealed that true resilience required a departure from the traditional migration methods that favored speed over security. It was determined that architectural complexity and fragmented designs often served as the greatest obstacles to maintaining a secure digital environment. By focusing on security-first engineering and the reduction of sprawl, organizations effectively transformed their cloud presence into a strategic asset that bolstered their overall defensive posture.
Experts emphasized that the alignment of cloud investments with specific organizational goals was the only way to ensure long-term stability. This approach moved the needle from reactive firefighting toward a state of continuous cyber assurance, where protection was an inherent part of the system’s DNA. These insights suggested that stakeholders who prioritized structural integrity over simple migration metrics achieved far greater reliability and readiness.
Conclusion or Final Thoughts
The evolution of cloud technology necessitated a complete rethink of how digital resilience was constructed and maintained. It became clear that the most successful organizations were those that treated security as an engineering discipline rather than a peripheral administrative task. This shift allowed for the creation of robust environments that supported innovation without sacrificing the safety of critical data or the continuity of essential services.
Looking forward, the focus should remain on refining these engineering practices to stay ahead of increasingly capable adversaries. Organizations are encouraged to audit their existing cloud footprints to identify areas where complexity has obscured vulnerability. By committing to a mission-aligned strategy, leaders can ensure that their digital transformation efforts continue to provide a competitive advantage while standing firm against the challenges of a volatile technological landscape.