The shifting landscape of modern cybersecurity now dictates that organizations must prioritize identity as the real perimeter rather than relying on legacy firewalls that attackers simply bypass using stolen but valid sign-in credentials. As the industry navigates the complexities of the current year, the traditional focus on hardening internal networks and patching software vulnerabilities has proven insufficient against adversaries who have mastered the art of masquerading as legitimate users. This reality has ushered in a necessary transition toward an identity-centric security model, where the primary objective is no longer just keeping unauthorized users out, but continuously verifying the intent of those who have already entered. The convergence of Privileged Access Management (PAM) and Identity Threat Detection and Response (ITDR) represents the most significant shift in defensive strategy in recent years. By integrating these once-distinct disciplines, enterprises are establishing a Unified Identity Defense Layer that provides the visibility and control required to maintain organizational resilience. This synthesis is not merely a technological upgrade but a fundamental requirement for any entity seeking to thrive in a world where the distinction between a trusted employee and a sophisticated threat actor has become dangerously blurred.
The Rising Dominance of Identity-Driven Intrusions
Current threat intelligence reports indicate that approximately 30% of all successful cyberattacks now involve the exploitation of legitimate credentials to gain unauthorized entry into corporate environments. This trend highlights a critical shift in attacker methodology; instead of searching for complex technical exploits or zero-day vulnerabilities, modern adversaries prefer the path of least resistance by obtaining valid usernames and passwords through phishing, social engineering, or the dark web. When an attacker possesses a functional credential, they do not need to break into a system; they simply sign in, effectively bypassing the multi-million dollar perimeter defenses that many organizations still rely upon. This evolution has rendered static security measures increasingly obsolete, as traditional tools struggle to identify a “malicious” login that looks identical to a standard user session. Consequently, the focus for security teams has shifted toward implementing dynamic, behavioral-based defenses that can scrutinize activity after the point of authentication, ensuring that the legitimacy of a session is verified through continuous observation rather than a single check.
The primary objective for 2026 and beyond involves achieving true identity resilience, which is defined as the capability of an organization to maintain secure and continuous operations even when specific user credentials have been compromised. Achieving this state requires a move away from the traditional “point-in-time” security checks that characterized previous decades. Instead, security models are evolving to incorporate a philosophy of constant assessment, where every action taken by an identity is evaluated against historical norms and risk profiles. This approach ensures that even if an initial perimeter is breached by an attacker with valid credentials, their ability to cause damage is severely restricted. By limiting lateral movement and flagging anomalous behaviors in real-time, organizations can effectively neutralize threats before they escalate into full-scale data breaches. This shift toward identity resilience is now recognized as the cornerstone of modern defensive architecture, providing a safety net that protects critical assets from the inevitability of human-centric vulnerabilities and credential theft.
Deconstructing the Limitations of Traditional Access Control
Privileged Access Management has served for years as the gold standard for controlling sensitive accounts, focusing primarily on the functions of authentication, credential vaulting, and the enforcement of the principle of least privilege. These systems are exceptionally proficient at ensuring that only pre-authorized personnel can access specific high-value systems, often utilizing just-in-time (JIT) access to minimize the duration of risk exposure. However, as the threat landscape has matured, the inherent limitations of standalone PAM solutions have become more apparent to security professionals. These platforms act primarily as gatekeepers; they are highly effective at validating the right of a user to enter a system, but they generally lack the deep, continuous visibility required to monitor what that user actually does once they have successfully passed the initial checkpoint. This creates a functional gap where a user could be granted access legitimately but then proceed to perform actions that fall outside their typical job responsibilities or authorized scope.
This particular limitation means that a standard PAM deployment often fails to distinguish between a legitimate administrator performing a routine maintenance task and a threat actor who is utilizing a stolen session to move laterally through the network. Because the PAM system views the session as “valid” based on the initial successful authentication, it lacks the behavioral context needed to detect subtle signs of data exfiltration or unusual query patterns that deviate from established norms. This visibility gap creates a dangerous blind spot that sophisticated attackers have learned to exploit, allowing them to remain persistent and undetected within a network for extended periods. Without the ability to monitor the ongoing intent and behavior of a privileged user, the organization remains vulnerable to any actor who can successfully navigate the initial authentication process. This realization has driven the need for a more comprehensive approach that combines rigorous access control with real-time detection capabilities to ensure that every session is monitored from inception to termination.
Implementing ITDR as a Dynamic Response Layer
Identity Threat Detection and Response (ITDR) has emerged as the necessary evolution to address the fundamental shortcomings found in standalone access management solutions. While traditional tools manage the “who” and the “what” of access, ITDR focuses explicitly on the “how” and the “why” of subsequent activity by maintaining a constant watch over the entire identity ecosystem. This technology works by establishing a granular behavioral baseline for every identity within the network, including human users, service accounts, and machine identities. By analyzing vast amounts of telemetry data, ITDR systems can identify the subtle patterns that define normal operation for a specific role or system. This continuous monitoring allows for the immediate identification of deviations, such as a user accessing a database they have never interacted with before or attempting to execute commands from a geographic location that does not align with their typical profile.
When the ITDR component identifies a significant anomaly, it provides the mechanism to trigger an automated and immediate response, which is a critical capability in the current high-velocity threat environment. Instead of waiting for a human analyst to review a log entry hours or days later, the system can take proactive steps such as terminating active sessions, forcing a password reset, or flagging the account for an immediate security review. This layer of security ensures that every action taken by an identity is under constant scrutiny, providing the necessary telemetry to stop an intrusion in its tracks before an attacker can reach their final objectives. By layering this detection and response capability over traditional access controls, organizations can create a more resilient defense that accounts for both the validity of the credential and the legitimacy of the behavior, effectively closing the gaps that attackers have historically used to hide their presence.
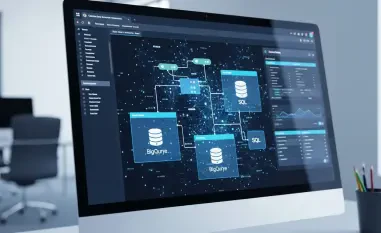
Building Synergy Through Converged Identity Platforms
The integration of PAM and ITDR into a single, converged model represents a strategic shift that creates a closed-loop security environment, significantly reducing the operational burden on security teams. In a traditional environment, these two functions often operate in silos, with separate management consoles and disconnected data streams, which can lead to “tool sprawl” and delayed response times. However, when these capabilities are unified, they work in tandem to create a cohesive defense. For example, if a user is granted privileged access through the PAM component but then begins to perform an unusual volume of data downloads, the ITDR component detects this deviation from the baseline immediately. Because the systems are linked, the ITDR can automatically signal the PAM tool to revoke the user’s privileges or rotate their credentials in a matter of seconds. This seamless communication ensures that the response is as fast as the threat, preventing potential damage before it can manifest.
This synergy transforms security from a series of disconnected, static checks into a proactive and intelligent response system that operates at machine speed. Such a consolidated approach allows organizations to move away from a reactive posture, where they are constantly trying to catch up with attackers, to a state of constant and automated vigilance. By combining strict entry controls with persistent behavioral oversight, enterprises can protect against both external threats and internal misuse more effectively than ever before. Furthermore, this unified model simplifies compliance reporting and forensic investigations by providing a single, authoritative source of truth for all identity-related activities. The ability to correlate a specific access grant with the subsequent actions taken during that session provides security analysts with the deep context needed to make informed decisions and refine access policies based on actual observed threat patterns rather than theoretical risks.
Evidence From Recent Large-Scale Security Breaches
Real-world incidents occurring earlier this year have provided a stark reminder of the dangers associated with relying solely on traditional access controls. A primary example is the significant breach involving a major national finance ministry, where attackers successfully bypassed all technical exploits and perimeter defenses by using stolen credentials belonging to a high-ranking civil servant. This unauthorized access allowed the threat actors to enter a national bank account registry, leading to the potential exposure of personal data for over a million citizens. Because the attacker utilized “valid” credentials that had been properly vaulted and authenticated, the standalone access management systems in place did not flag any initial red flags. The system saw a legitimate user performing tasks with authorized credentials, which allowed the intrusion to persist long enough for significant data to be accessed.
This specific incident serves as a definitive case study for why privileged access management, when utilized in isolation, is no longer sufficient for modern security requirements. A unified PAM and ITDR system would have been necessary to detect the subtle behavioral anomalies that always accompany unauthorized data access, such as unusual query volumes or access to specific records that did not align with the civil servant’s historical work patterns. The lesson for organizations today is clear: without the capability to analyze the behavior behind the credential, any entity remains vulnerable to an actor who can successfully “log in.” The ability to distinguish between a legitimate user and a malicious actor using that user’s identity is the critical missing link that only the convergence of detection and response can provide. This case has accelerated the adoption of integrated identity platforms across both the public and private sectors as the only viable defense against credential weaponization.
Navigating Global Compliance and Security Frameworks
The transition toward a unified identity defense is increasingly becoming a regulatory mandate across the globe rather than just a strategic internal choice for businesses. Major international frameworks, such as the updated Zero Trust guidelines and the latest iterations of the NIST Cybersecurity Framework, now explicitly prioritize identity management as a foundational element across all security functions. These standards emphasize the core tenet of “never trust, always verify,” which requires the continuous validation of user intent and behavior that only a combination of PAM and ITDR can effectively deliver. Organizations that fail to implement these integrated controls find it increasingly difficult to meet the rigorous auditing requirements of these frameworks, as auditors now look for proof of continuous monitoring and automated response capabilities rather than just static access lists.
Furthermore, international regulations like the General Data Protection Regulation (GDPR), the NIS2 Directive, and the Digital Operational Resilience Act (DORA) for the financial sector have set a high bar for technical security measures and incident response. These mandates require organizations to demonstrate “state-of-the-art” protection and the ability to rapidly mitigate risks to sensitive data and critical infrastructure. Unified identity platforms facilitate this compliance by providing the comprehensive forensic trails and automated mitigation tools necessary to satisfy regulatory inquiries. In the current environment, compliance is defined by an organization’s ability to prove that it maintains constant oversight of all identities and can respond to threats within minutes. By adopting a converged model, enterprises not only enhance their security posture but also ensure they remain aligned with the evolving legal landscape, avoiding the heavy penalties and reputational damage associated with non-compliance.
Strategic Imperatives for Identity Defense Architecture
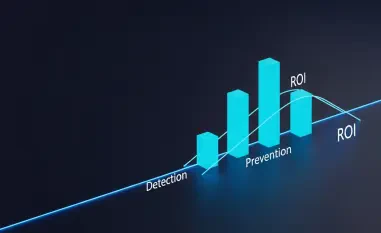
The convergence of identity technologies provides modern security teams with four primary advantages that are essential for navigating today’s complex threat environment. First, it offers full attack lifecycle coverage, ensuring protection from the moment of initial entry to the final logout. Second, it eliminates common blind spots regarding machine identities and service accounts, which are frequently overlooked by traditional tools but are now high-priority targets for attackers looking to automate their intrusions. Third, the integration enables accelerated incident mitigation through the use of automation, allowing for the immediate termination of high-risk sessions without the delays inherent in manual human intervention. Finally, the data collected through this integrated approach supports intelligence-driven decision-making, providing the deep context needed for forensic investigations and the refinement of access policies based on actual threat patterns.
To effectively implement this new standard, organizations took several concrete steps over the past year to restructure their defensive architecture. Security leaders moved away from purchasing isolated point solutions, opting instead for integrated platforms that offer native ITDR capabilities within a robust PAM framework. This strategic shift allowed for the creation of more resilient service accounts and secured machine-to-machine communications that were previously vulnerable to lateral movement. By focusing on the behavior of every identity, whether human or non-human, security teams successfully reduced the mean time to detect and respond to credential-based threats. This proactive approach ensured that even in instances where a credential was stolen, it could not be successfully weaponized against the organization. Moving forward, the industry has recognized that a unified identity defense is the only sustainable path toward operational resilience in an era where attackers no longer need to find a way in—they simply need to find a way to log in.