The rapid migration of enterprise workflows into the web browser has created a paradox where the traditional firewall, once the ultimate arbiter of network security, now stands largely bypassed by the very traffic it was designed to govern. As modern employees spend the vast majority of their working hours within SaaS platforms and cloud-native interfaces, the classic IP-based perimeter has effectively dissolved. This shift has necessitated a fundamental reconsideration of how security is enforced. Firewall-Native Security Service Edge (SSE) emerges not as a replacement for the existing stack, but as a critical architectural upgrade. It attempts to resolve the “visibility gap” by injecting session-layer intelligence into established network defenses, ensuring that security policies follow the user’s intent rather than just their destination.
The Shift to Session-Aware Security Architectures
The emergence of Firewall-Native SSE is a direct response to the fundamental shift in how modern enterprises operate. Historically, network security was built around a rigid perimeter where the firewall acted as a gatekeeper for IP-based traffic. However, as business workflows migrated to the cloud and the web browser became the primary interface for work, traditional network-layer defenses began to lose their efficacy. This transition happened so rapidly that many organizations found themselves defending a perimeter that no longer contained their most valuable data or their most frequent interactions.
This technology evolved to bridge the visibility gap created by encrypted HTTPS traffic and the proliferation of Software-as-a-Service (SaaS) platforms. While traditional SSE solutions attempted to solve this by replacing existing infrastructure, Firewall-Native SSE introduces a more integrated approach. Its core principle involves upgrading established network defenses with session-layer intelligence, allowing security teams to inspect the context of web interactions without abandoning their existing hardware investments. By moving the focus from the packet level to the session level, organizations can finally see what is happening inside the encrypted tunnel, rather than just knowing that a tunnel exists.
Technical Architecture and Core Functionalities
Session-Level Traffic Inspection
One of the primary features of Firewall-Native SSE is its ability to perform deep inspection at the session layer. Unlike traditional firewalls that only see Port 443 traffic as a monolithic block of encrypted data, this technology deconstructs the session to understand user intent. It functions by intercepting browser activity and web requests in real-time. This allows the system to distinguish between a user simply visiting a website and a user attempting to upload sensitive proprietary data to a personal cloud storage account.
The significance of this inspection lies in its performance. It matches cloud-native speeds while ensuring that security policies are applied to the actual content of the communication rather than just the destination. Because the inspection happens at the session layer, the system can apply granular rules—such as allowing a user to view a document but preventing them from downloading it—without the latency typically associated with older proxy-based systems. This creates a more fluid experience for the end-user while maintaining a much tighter security posture for the organization.
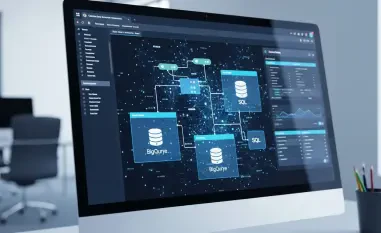
Agentless Deployment and Infrastructure Integration
A significant technical component of the firewall-native approach is its agentless delivery model. Instead of requiring invasive software on every endpoint, the system integrates directly with existing firewall environments from major providers like Palo Alto Networks or Fortinet. This integration allows for a non-disruptive overlay that intercepts traffic at the network edge. For IT departments, this is a game-changer; it removes the logistical nightmare of deploying, updating, and troubleshooting agents across thousands of diverse devices, including unmanaged or “bring your own” hardware.
This architecture’s significance lies in the massive reduction of operational complexity, enabling enterprises to gain SSE capabilities—such as Cloud Access Security Broker (CASB) and Secure Web Gateway (SWG) functions—without a “rip and replace” overhaul. By leveraging the existing network path, the firewall-native model ensures that security is baked into the connection itself. This approach turns the firewall into a more intelligent sensor and enforcement point, effectively extending its life and utility in an era where it might otherwise have become obsolete.
Emerging Trends in Session-Centric Defense
The field is currently influenced by a shift toward infrastructure-aware security. Industry behavior is moving away from the platform fatigue caused by constant hardware replacement cycles and toward modular security overlays. A key innovation in this space is the development of specific monitoring for WebSockets and browser extensions, which have become common vectors for credential harvesting. Because these elements often operate outside the view of traditional inspection tools, having a session-aware layer that can monitor their behavior in real-time is becoming a prerequisite for modern defense.
Furthermore, there is a growing trend of “just-in-time” security, where inspection layers are activated dynamically based on the risk profile of the application being accessed. For instance, a connection to a known, low-risk internal portal might receive minimal inspection to preserve performance, while a connection to a newly registered domain or a high-risk AI platform triggers full session deconstruction. This reflects a more nuanced approach to user productivity and data protection, moving away from the “all or nothing” security models of the past decade.
Real-World Applications and Sector Impact
Firewall-Native SSE is being rapidly deployed across sectors that handle sensitive data, such as finance, healthcare, and legal services. In these industries, the technology is used to enforce strict Data Loss Prevention (DLP) policies within web-based collaboration tools. For example, a legal firm can allow its partners to use cloud-based document editing platforms while ensuring that no client-privileged information is ever pasted into an unauthorized chat window. This level of control was previously impossible without a heavy-handed approach that often hindered professional collaboration.
A notable implementation is in the governance of Generative AI (GenAI) platforms. Organizations use Firewall-Native SSE to provide a “middle path” for AI adoption—allowing employees to use tools like ChatGPT while the security layer automatically redacts sensitive Personal Identifiable Information (PII) or intellectual property before it reaches the AI’s servers. This use case is particularly transformative for R&D-heavy industries that want to leverage AI for efficiency without risking trade secret exposure. It essentially creates a “safety glass” between the corporate data and the public AI, allowing for innovation without the associated catastrophic risks.
Technical Challenges and Implementation Hurdles
Despite its advantages, the technology faces certain hurdles. A primary technical challenge is maintaining low latency during deep packet inspection of high-volume encrypted traffic. While the firewall-native model is more efficient than traditional backhauling, any additional inspection layer introduces potential performance bottlenecks. Enterprises with massive global footprints must carefully calibrate their session inspection rules to avoid “lag” that could lead to users attempting to bypass security controls altogether.
Furthermore, market adoption can be slowed by the perceived complexity of integrating cloud-based session layers with legacy on-premises hardware. Not all legacy firewalls are immediately compatible with the latest overlay technologies, and some organizations may still face a partial upgrade cycle. Regulatory hurdles regarding data privacy also persist, as session-level inspection involves handling decrypted content. Ongoing development efforts are focused on improving localized processing—where data is inspected but never stored—and enhancing automated policy engines to mitigate these limitations and streamline the user experience.
Future Trajectory and Industry Evolution
Looking ahead, Firewall-Native SSE is poised to become the standard for hybrid work environments. Future developments will likely involve the integration of machine learning to predict anomalous session behavior before a data breach occurs. Instead of reacting to a policy violation, the system might proactively throttle a session if it detects patterns consistent with data exfiltration or account takeover. This transition from reactive to predictive security will be the next major milestone for the technology.
We can also expect to see a deeper convergence between the browser and the security stack, where the session-aware layer becomes a native part of the enterprise network fabric. Long-term, this technology may render the distinction between network security and application security obsolete. As the browser becomes the operating system for the modern worker, the defense mechanism must reside where the work happens. This evolution suggests a future where the security posture is entirely fluid, following the data and the user session across any network or device.
Summary of Findings and Assessment
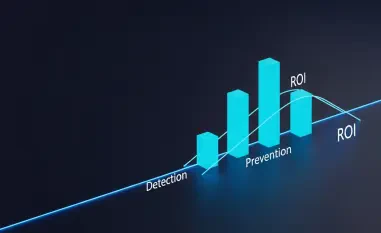
The analysis of Firewall-Native SSE demonstrated a pragmatic shift in how organizations secured their digital assets. It was observed that the technology successfully closed the “visibility gap” by providing deep, session-aware inspection without requiring the total abandonment of existing network investments. The transition toward agentless, firewall-integrated deployment models proved to be a critical factor in reducing operational friction and accelerating the adoption of CASB and SWG functions. Moreover, the implementation of this technology provided a viable pathway for the safe adoption of Generative AI tools, allowing companies to balance innovation with data integrity.
For enterprises moving forward, the focus must shift toward optimizing these session-aware layers to handle increasingly complex web architectures and higher traffic volumes. The verdict for security leaders was clear: Firewall-Native SSE represented a necessary evolution that respected the reliability of legacy systems while introducing the sophistication required for a browser-centric world. Organizations should have prioritized integrating these session-aware overlays into their existing infrastructure to ensure that their defenses remained relevant as the perimeter continued to vanish. This approach provided a resilient foundation that was both cost-effective and capable of adapting to the next generation of web-based threats.